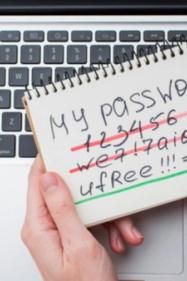
Often, when an individual needs to create a new password, they will rack their brains and choose personal information that relates to them, then modify it by changing elements or adding special characters.
Unfortunately, this is a bad strategy: all of your passwords should be generated randomly. We will see why in this article.
1) OSINT: The Hacker's Research Phase
When a hacker gears up for a moderately sophisticated attack, the first step they embark upon is called OSINT — Open Source Intelligence. This step involves scouring publicly available (open source) information about their target(s).
The hacker closely examines the profile of the victim to gather personal details like the names of family members, age, hobbies, etc. Such information is not only useful to craft plausible pretexts for phishing emails but also to potentially guess their passwords.
Consider a Facebook post from March 26, 2020, as an exemplary goldmine for hackers. The post is a chain message urging users to share it on their own wall, revealing a plethora of personal information.
From such posts, a hacker could discern details like the individual's age, favorite sport, marital status, and a wealth of other information. This treasure trove of data can be harnessed to construct an attack narrative or guess their passwords.
While this post is an extreme example, even if you don't regularly share such detailed posts, you might still be giving away the same information but in a more fragmented manner.
By aggregating information you've shared across various social platforms, a hacker can piece together a comprehensive profile about you. For instance, on LinkedIn, they might find data about your past jobs or colleague names, and on Instagram, details about your family, relationships, or vacation destinations.
If you don't use a randomly generated password, there's a high likelihood of a hacker using this collated information to crack it.
Once they've gathered enough intel, their next step is to generate a list of potential passwords to attempt to breach your private accounts.
II) How Does a Hacker Generate Potential Password Lists?
To create a password list, hackers often employ dictionary generation tools like Cupp. They'll input details about the victim, such as their name, birthdate, partner's name, employer, etc.
They can also incorporate keywords related to the target, like their favorite sport. Moreover, special characters can be appended. It's a common misconception that merely adding “!” or “.” at the end of a password makes it secure.
We tend to use similar special characters in our passwords, which simplifies the hacker's task.
Using Cupp, hackers can also opt to append random numbers to the password list and activate the 'leet mode'.
This mode replaces letters with numbers or symbols, like 'a' with '@' or '4', 'E' with '3', 'T' with '7', and 'L' with '1'. Many people mistakenly believe that by making such tweaks, they're securing their passwords.
As you might discern, these methods are ineffective against a determined hacker. By tweaking all the aforementioned parameters in Cupp, a hacker can produce a list with thousands of potential passwords, as illustrated in the image below.
Such passwords can easily be tested on poorly secured systems or databases compromised during a breach.
III) Generate Passwords Randomly with Password Managers
Now that we've understood how effortlessly a hacker can guess your passwords, let's discuss a solution: password managers.
We've penned an article to guide you in effectively managing your passwords.
Password managers safely store your passwords. All you need to remember is a single “master” password that grants you access to all of your stored passwords.
Many of these tools offer not just storage, but also password generation. While some come with a price tag, others are freely accessible.
Conclusion
In summary, the random generation of passwords is crucial for securing your accounts.
Relying on personal details easily found online makes your password vulnerable to dictionary attacks using tools like Cupp.
Broadly speaking, to shield yourself, it's vital to be wary of the information you disclose online. Additionally, regularly check and adjust your online profile privacy settings to control the visibility of your shared data on social media.