Abnormal Intelligence documented VENOM, a previously unknown PhaaS platform behind a five-month campaign targeting C-suite executives across 20+ industries, systematically bypassing MFA to establish persistent Microsoft 365 access.
Key Takeaways
- MFA is not a final line of defense here. VENOM operates through adversary-in-the-middle relays and Microsoft's own Device Code flow, not by exploiting MFA, but by operating within it. Standard MFA does not prevent compromise.
- C-suite executives are the deliberate target. 60% of recipients hold a C-level, President, or Chairman title, selected by name, not harvested at random. Each compromised account becomes a launchpad for BEC, fraudulent wire transfers, and lateral phishing.
- The attack surface is shifted to unmanaged devices. QR code delivery moves the interaction from corporate endpoints (where security controls apply) to personal mobile phones, where they don't.
- A phishing reset won't save you. In Device Code mode, captured refresh tokens survive password resets entirely. Remediation requires explicit session and token revocation in Entra ID; a step absent from most standard incident response runbooks.
Attack Timeline
STEP 1
Spear-phishing email deliveryThe target receives a SharePoint document-sharing notification, dynamically personalized from their own email domain. Sender address, company name, and footer branding are all auto-generated to appear internal. The QR code embedded in the email is rendered entirely from Unicode characters; no image file, nothing for scanners to process. |
|
STEP 2
QR code scan on a personal deviceScanning shifts the session from a managed corporate endpoint to the target's personal mobile phone, bypassing corporate proxies and endpoint protection. The target's email is double Base64-encoded in the URL fragment (a portion never transmitted to any server) making it invisible to proxy logs and URL reputation feeds. |
|
STEP 3
Verification gate filteringThe URL resolves to a fake bot-challenge page (impersonating Cloudflare or Microsoft Defender). Before anything loads, the gate silently screens visitors through User-Agent analysis, live IP reputation checks, hidden honeypot elements, and proof-of-work challenges. Security tools, sandboxes, and researchers are silently redirected to benign sites. Only real human targets pass through. |
|
STEP 4
Credential harvestingCleared visitors reach a Microsoft sign-in page generated in real time from their own identity provider, with their organization's logo, their email pre-filled, their actual federated IdP page. In AiTM mode, every credential and MFA code is relayed live to Microsoft's API as the target types. In Device Code mode, the target authenticates directly on microsoft.com and Microsoft delivers the tokens to the attacker's backend. |
|
STEP 5
Persistence establishedBefore the target's browser redirects, the platform registers an attacker-controlled MFA device on the target's Microsoft 365 account. In Entra ID logs, this appears as a |
Social Engineering at Every Stage: Impersonation, Urgency, and Trust
What makes VENOM stand out is not any single technical capability. It is how systematically every stage is engineered around human psychology.
- The initial lure borrows its authority from two sources: trusted internal infrastructure and familiar workflow friction. Impersonating SharePoint, Dropbox, Docusign, DHL, and UPS isn't accidental; these are platforms C-suite executives interact with daily, in contexts where reviewing a document or confirming a delivery feels routine rather than suspicious. The financial report theme adds a layer of urgency: executives expect to receive and act on financial documents quickly, often without double-checking sender details in a busy schedule.
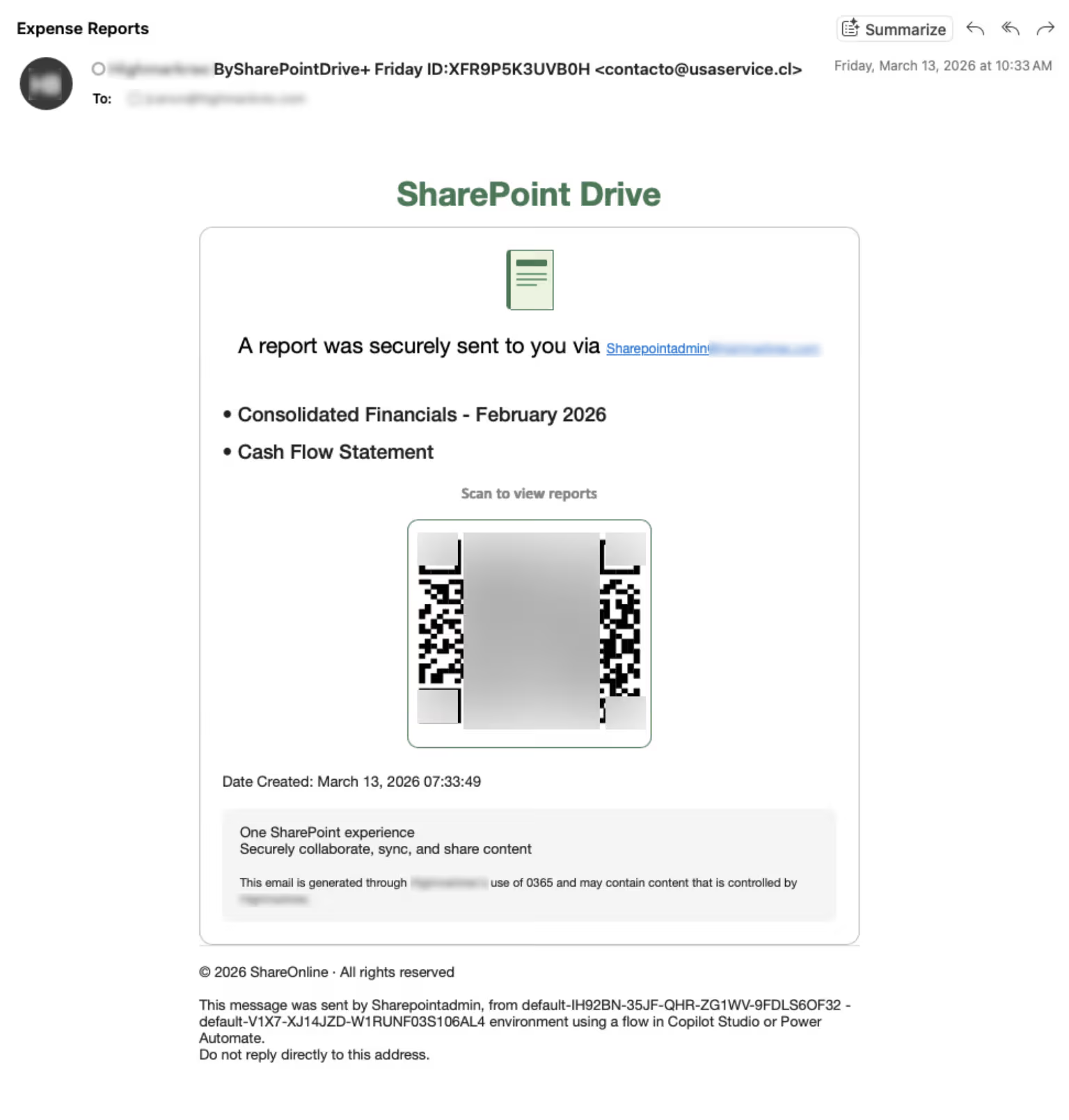
Example of malicious email impersonating SharePoint notification (Abnormal Intelligence)
- Personalization amplifies the effect. The sender address is generated from the target's own domain. The company name appears in the footer. The email reads as if it originated internally. This is not generic phishing: it is a message designed to look exactly like something the target's own organization would send.
- At the verification gate, the social engineering continues. The fake Cloudflare or Microsoft Defender challenge is a form the target has seen before, a routine web safety check. Completing it feels like normal browsing behavior, not a security red flag. The target is being asked to do something familiar, not something unusual.
The credential harvester carries this logic to its conclusion. The login page the target sees is not a static fake: It is a live mirror of their actual identity provider, complete with their organization's logo, their real federated login flow, and their email pre-filled. There is nothing visually inconsistent with a legitimate sign-in. The experience is indistinguishable from the real thing precisely because, in every visible respect, it is the real thing, relayed through an attacker-controlled middle layer.
In Device Code mode, the social engineering is even more subtle. The target is never shown a credential form at all. The lure frames the interaction as a Docusign document verification; familiar, low-friction, authority-backed. The "verification code" they copy and paste into microsoft.com is presented as a document access step, not an account authorization. The target performs a completely legitimate action on Microsoft's own infrastructure. The compromise lies entirely in where the resulting tokens end up.
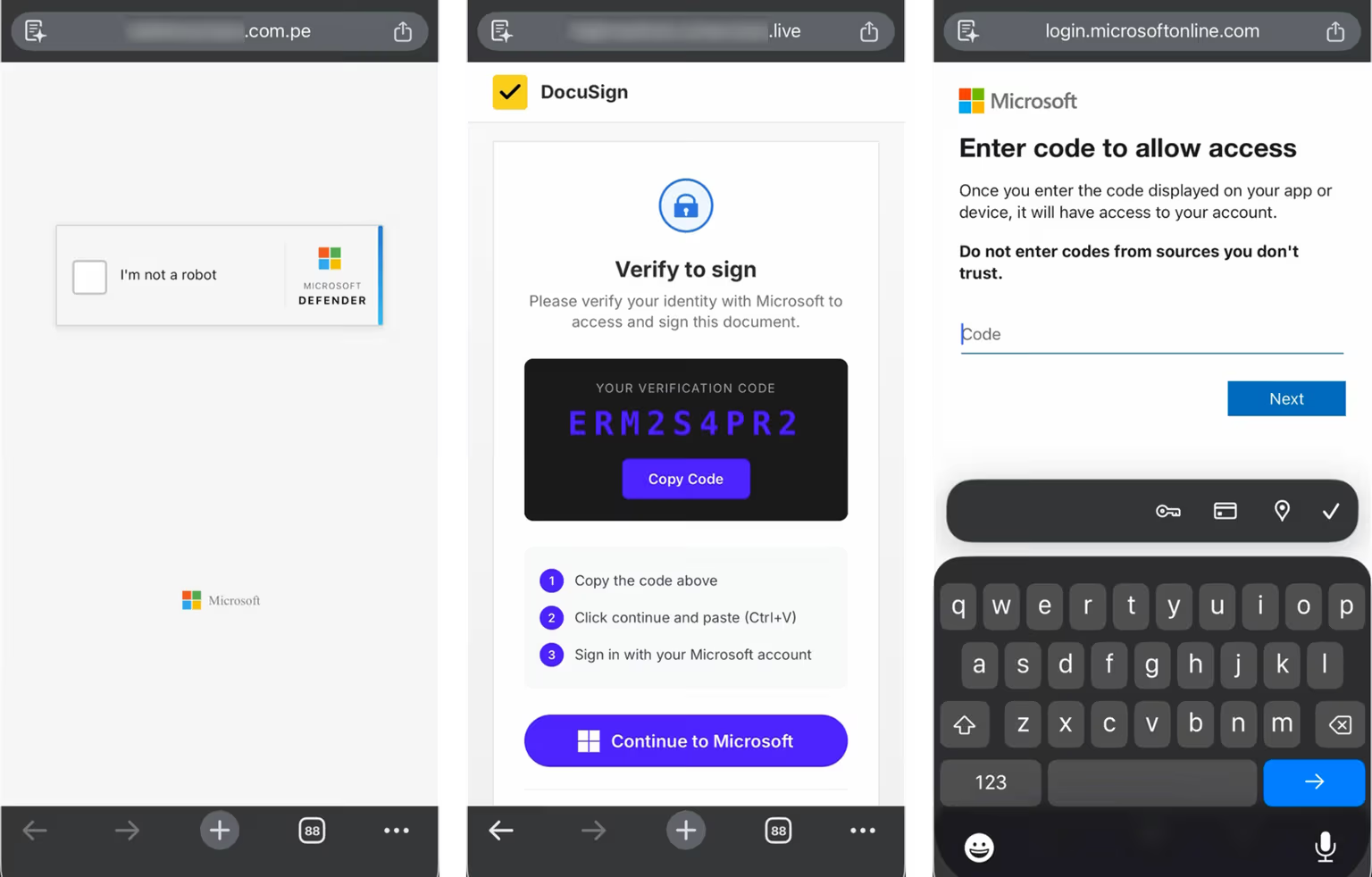
Device Code mode credential harvester flow (Abnormal Intelligence)
Together, these techniques exploit two of the most reliable levers in social engineering: authority (Microsoft, SharePoint, Docusign, internal branding) and familiarity (routine workflows the target performs every day without thinking). The attack does not ask targets to do anything unusual. It asks them to do things they already do, in a context constructed to make suspicion unnecessary.
Prevention and Remediation
VENOM is a technical operation built entirely on a human foundation. That means the most durable defenses are also human.
Train executives specifically, not generically.
Standard phishing awareness is not sufficient here. C-suite employees face a distinct threat profile targeted spear-phishing, QR code attacks, social engineering via voice and SMS) and need training calibrated to that reality. Arsen's Executive Protection program addresses exactly this gap, with tailored simulations and workshops designed for leadership exposure: vishing with voice cloning, double-barrel attacks, multi-vector scenarios. Executives who have seen these attacks simulated are far less likely to complete one by accident.
Simulate QR code attacks before attackers do.
QR code phishing is a growing vector specifically because it shifts the attack to unmanaged mobile devices outside corporate security controls. Arsen offers both a QR Code Phishing Test and a QR Code Phishing Simulation to measure exposure and build recognition before a real incident occurs.
Monitor for the threat signals VENOM leaves behind.
Arsen's Threat Monitoring capability tracks typosquatted and look-alike domains as well as data leaks linked to your organization — two of the input signals attackers use to build personalized lures. Catching exposed executive data early reduces the attacker's ability to craft convincing impersonations.
Harden your Microsoft 365 configuration.
On the technical side, organizations should restrict Microsoft's Device Code authentication flow via Conditional Access where it is not operationally required. Monitor Entra ID audit logs for SoftwareTokenActivated events with display name NO_DEVICE — the forensic signature VENOM leaves after enrolling a persistent authenticator. Incident response runbooks must include explicit revocation of all active sessions, token grants, and unauthorized MFA registrations in Entra ID. A password reset alone does not revoke a captured refresh token.
Layer simulations across all social engineering vectors.
VENOM combines phishing, QR code delivery, and trusted-brand impersonation into a single chain. Effective preparation requires the same breadth. Arsen's phishing simulation platform and security awareness training are built to address the full spectrum (including spear-phishing, business email compromise, and QR code attacks) so that no single technique goes untested.
Summary
Not reliably. VENOM uses two harvesting modes that defeat MFA through different mechanisms. In AiTM mode, credentials and MFA codes are relayed to Microsoft's live API in real time — the attacker captures the authenticated session as it is created. In Device Code mode, the target authenticates directly on Microsoft's infrastructure and Microsoft delivers the resulting tokens to the attacker. In both cases, MFA fires and completes normally; it does not prevent the compromise.
Executives hold the broadest access to sensitive financial data, strategic communications, and organizational authority. A compromised C-suite account is not just a credential theft — it is a trusted launchpad. From a CEO's mailbox, an attacker can initiate business email compromise, authorize fraudulent wire transfers, and send lateral phishing that carries inherent authority and is difficult to distinguish from legitimate communication.
Each email is programmatically generated and individually personalized from a single input — the target's email address. The sender domain is derived from the target's own organization, the company name appears in the footer, and the QR code is rendered entirely from Unicode characters with no image file. Every send also contains randomized HTML elements that ensure no two emails produce the same hash or string match, defeating signature-based detection.
The priority action is not a password reset. Because VENOM can capture OAuth refresh tokens that survive credential changes, affected organizations must explicitly revoke all active sessions, token grants, and MFA device registrations in Entra ID. Audit logs should be reviewed for
SoftwareTokenActivatedevents with the display nameNO_DEVICE. Standard incident response runbooks may not include these steps — they should be added proactively.
The most effective preparation combines targeted simulations with deliberate training. Executives specifically need exposure to the attack patterns they are most likely to face: spear-phishing with internal branding, QR code lures, and credential harvesting flows indistinguishable from legitimate sign-ins. Arsen's Executive Protection program is designed to deliver exactly this, alongside OSINT-based exposure monitoring to detect threats before they escalate.