Recent CISO surveys point to a more complex threat landscape: AI is accelerating attacks and amplifying risk, even as it offers powerful defensive capabilities when used effectively. At the same time, operational and compliance demands continue to rise, with increased accountability for everyone. Annual training, generic phishing simulations, and incident-based metrics are no longer sufficient. Here’s why they fall short and what a mature, modern security awareness program should look like instead.
Key takeaways
- Phishing is the entry point for 90% of cyber attacks. Yet, most organizations still address it with tools that haven't changed in a decade.
- Awareness and preparedness are not the same thing. Employees can know exactly what phishing looks like and still fall for it under pressure.
- Vishing and multi-channel social engineering are growing fast, and almost no one is training for them.
- Measuring incident counts tells you what went wrong. Measuring behavior tells you what's about to.
- A resilient security posture is built on continuous, practical, and contextual training; not annual compliance cycles.
1. Replace Generic Phishing Templates with Role-Based, Adaptive Simulations
OLD WAY
Same phishing template sent to the whole company every quarter.
NEW WAY
AI-generated, role-specific scenarios that adapt based on past performance and real attack patterns.
Not all employees face the same threats. An HR manager is far more likely to open a fake CV attachment than someone from the finance team. A finance employee is a prime target for a fraudulent wire transfer request. A member of the executive team will be impersonated more often than they'll be targeted by mass phishing.
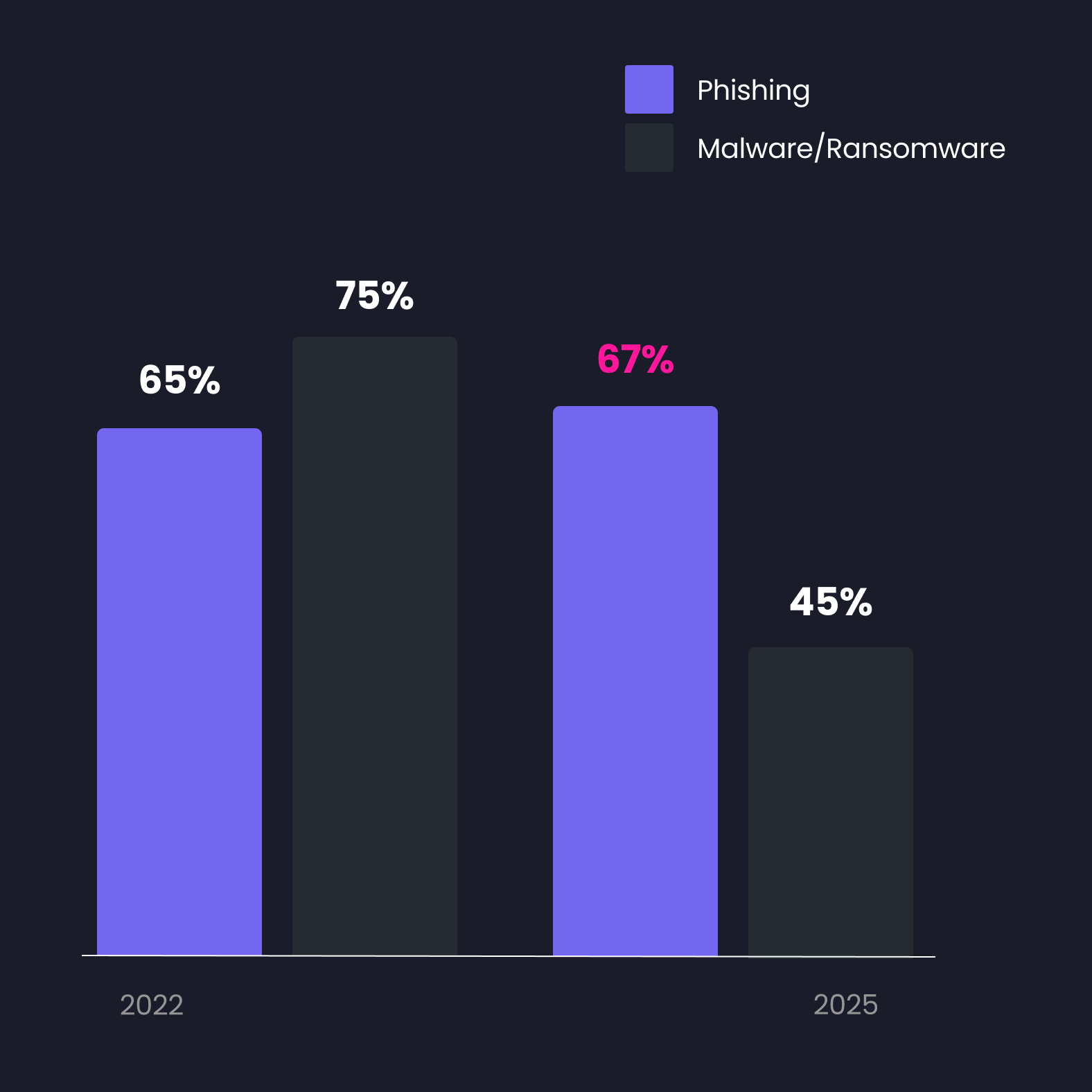
Phishing remains a top concern for CISOs, while malware/ransomware diminish.*
Generic simulations don't account for this. They train employees to recognize the format of your internal security tests; not to detect real attacks. Real attackers tailor their approach to the target. Phishing simulations should too.
Effective simulation programs vary templates continuously, use pretexts relevant to each department, adjust difficulty based on individual results, and use every simulation outcome to inform the next one. The click rate matters less than the trend: Are specific teams improving? Are certain roles consistently underperforming? That's the data that drives useful action.
2. Move from Once-a-Year Training to Continuous, Contextual Learning
OLD WAY
Annual e-learning module, same content for everyone.
NEW WAY
Continuous micro-training delivered when and where decisions actually happen.
There's a fundamental problem with annual security awareness training: people forget. The forgetting curve is well-documented. Without reinforcement, most of what employees learn disappears within days. Running a training session once a year and expecting it to change behavior twelve months later isn't a security strategy. It's a compliance exercise.
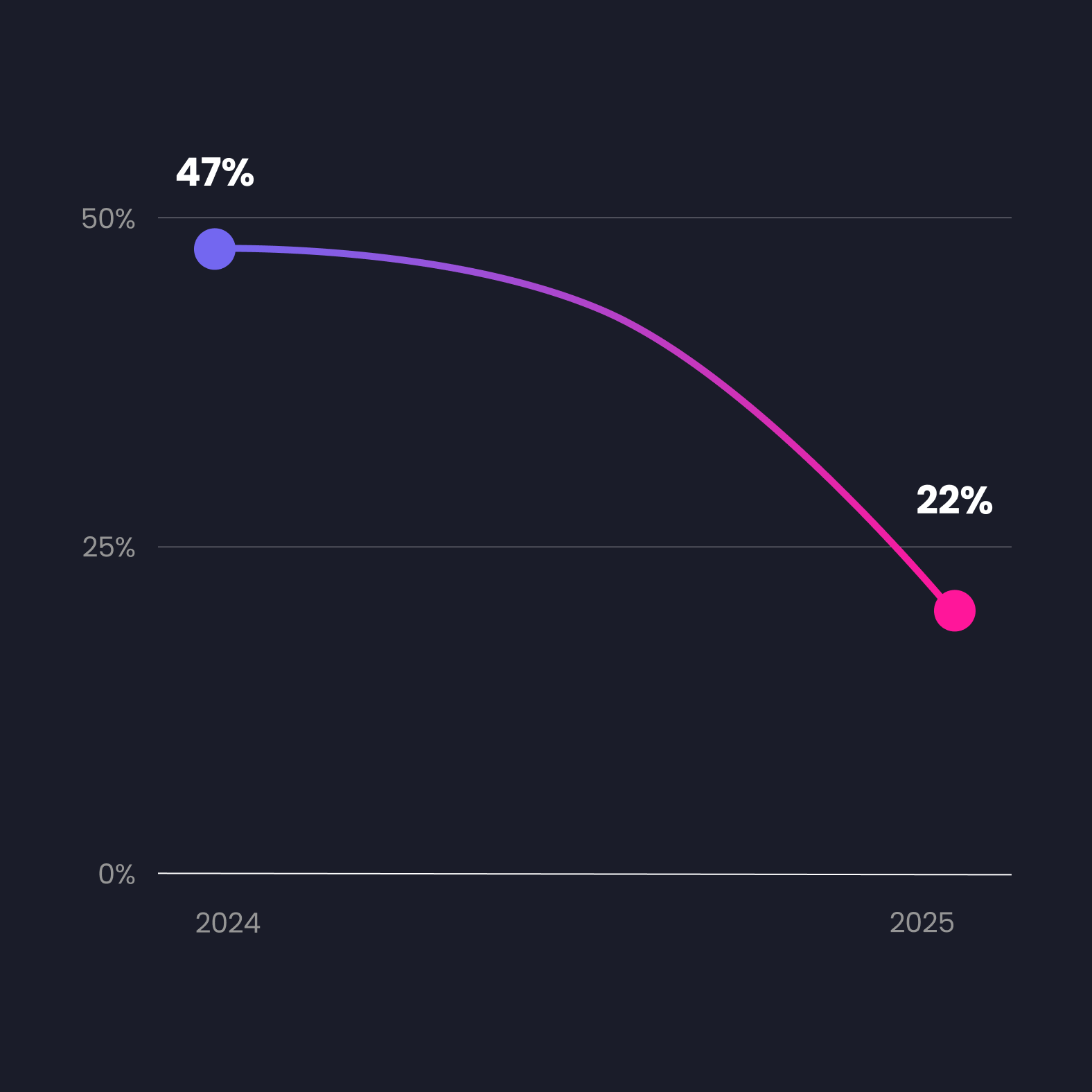
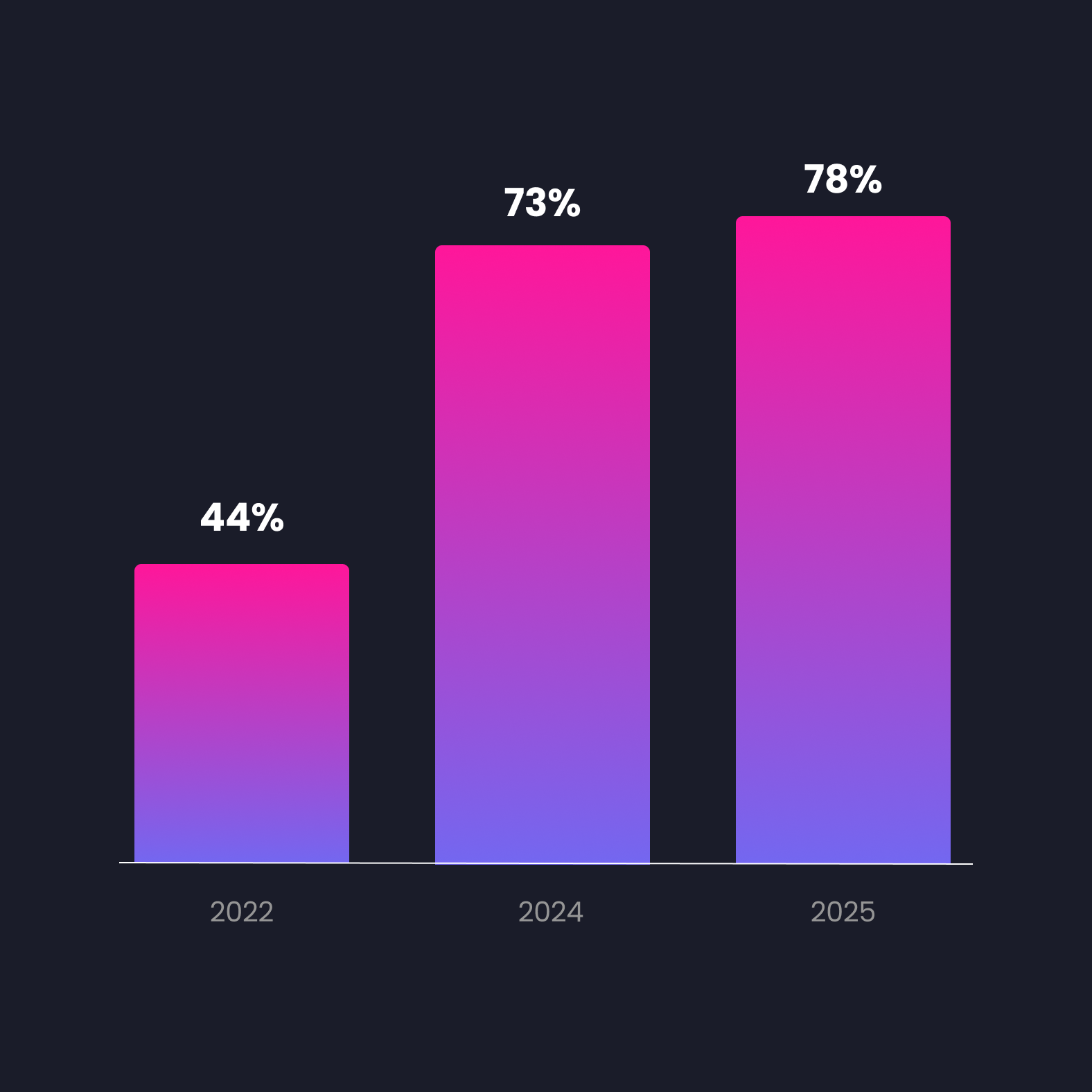
CISOs confidence in staff competency diminishes.*
What works is continuity. Short, relevant, and well-timed training moments that employees encounter regularly, not as a one-off event, but as part of how they work. This means contextual nudges when they're about to take a risky action, role-specific content that reflects the threats they're actually likely to face, and simulations that repeat often enough to build real reflexes.
The goal isn't to have employees who can define phishing. It's to have employees who make the right call at 4pm on a Friday when they're distracted and someone is pushing them to act fast.
According to the 2026 NASCIO-Deloitte Cybersecurity Study, only 22% of state CISOs believe their cybersecurity professionals have the competencies needed to face current threats, down from 47% in 2024. That drop reflects a training design problem.
3. Add Vishing to Your Simulation Program Before Attackers Get There First
OLD WAY
Email-only phishing simulations, no coverage of phone-based attacks.
NEW WAY
Multi-channel simulations including voice phishing, with scenario diversity and a recurring cadence.
Vishing (voice phishing) exploits something email-based training simply doesn't address: the way people respond under real conversational pressure. When someone calls you, the interaction is immediate, emotional, and hard to pause. Attackers know this. They use urgency, authority, and familiarity to push employees into disclosing credentials or taking actions they'd never approve via email.
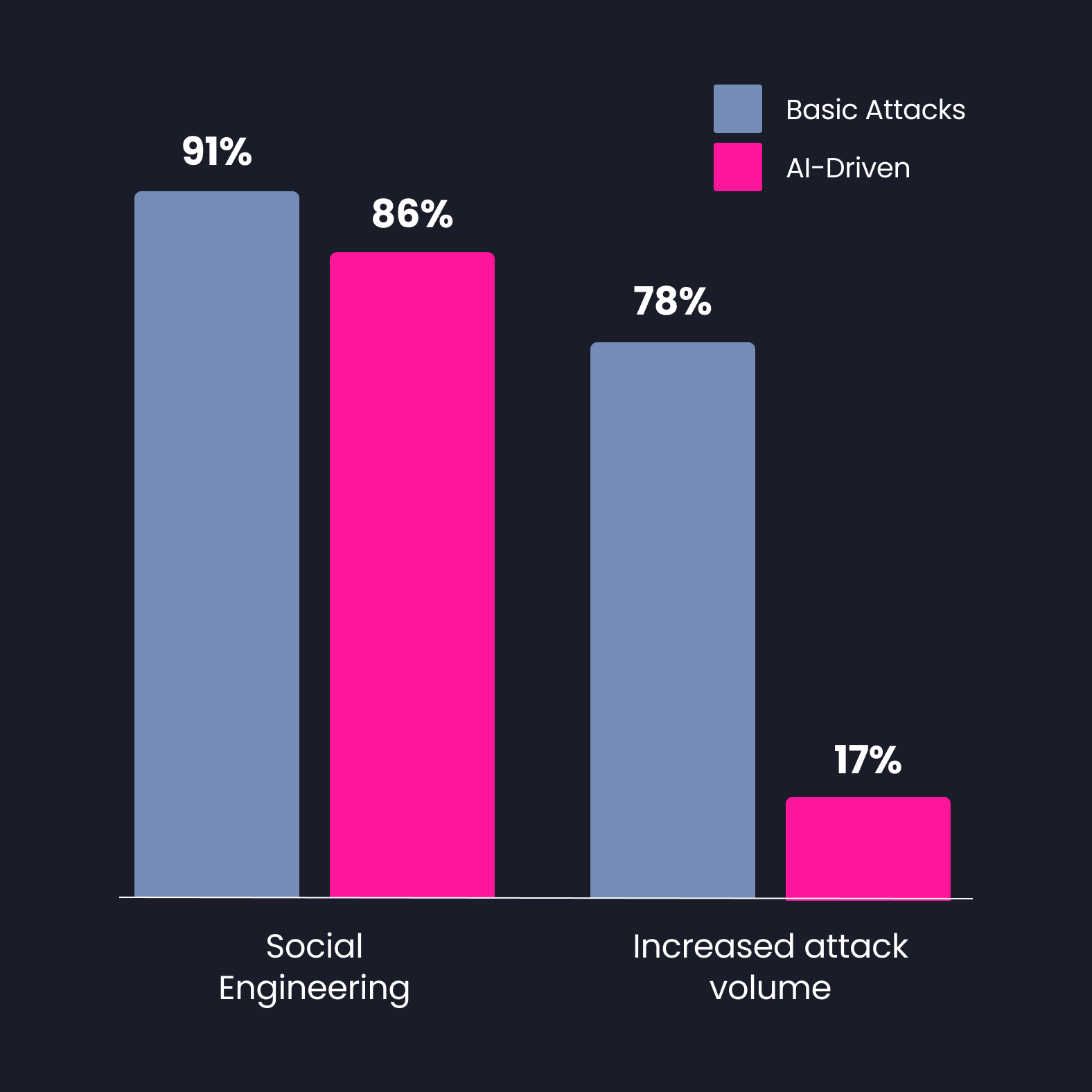
AI-driven threats is seen as more and more concerning, especially regarding social engineering.*
A key principle of social engineering is putting the victim into an emotional state, one that bypasses the rational thinking that e-learning content is designed to activate. This means employees can have perfect theoretical knowledge about vishing and still fail when a social engineer calls them. The emotional pressure of the interaction overrides the training they received in a calm, controlled setting. This is why practical simulation is non-negotiable.
AI voice cloning has made this significantly worse. It is now possible to convincingly impersonate a CEO, a finance director, or an IT support agent with minimal effort. A good vishing awareness program combines periodic simulations (at minimum quarterly, ideally monthly for high-risk roles) with real scenario diversity. Using the same script and the same pretext each time trains employees to recognize your simulation, not vishing in general. Vary the scenarios, the timing, the caller identity, and the pretext. Then debrief. Talk to your best and worst performers, both will tell you something useful about where your program needs to improve.
According to the Splunk CISO Report 2026, 91% of CISOs expect AI to increase the realism and effectiveness of social engineering attacks, making voice-based impersonation one of the most anticipated threat vectors to scale in the near term.
4. Stop Measuring Incidents and Start Measuring Decisions
OLD WAY
Quarterly incident report as the main proof of program effectiveness.
NEW WAY
Behavioral metrics (click rates by role, warning override rates, time-to-report) as leading indicators of risk.
Here's a scenario: your organization recorded two data loss incidents last year. On paper, that looks fine. But underneath that number, employees overrode security warnings hundreds of times. Most were ignored. A few led to the incidents you recorded. The rest were near-misses no one tracked.
Measuring effectiveness is a top CISO initiative in 2026.*
Incident count is a lagging metric. It tells you about damage that already happened. Behavioral data tells you where risk is accumulating before it becomes an incident. Which departments are consistently clicking on simulations? Who overrides security prompts regularly? How long does it take teams to report a suspicious email? These signals are your real risk map.
Phishing risk assessment should also account for consequences, not just frequency. A click from an employee with limited system access carries a very different risk profile than a click from someone on the executive committee with full network rights. Mapping both probability and potential severity gives you a realistic picture of your exposure, and helps you prioritize where to focus your training budget.
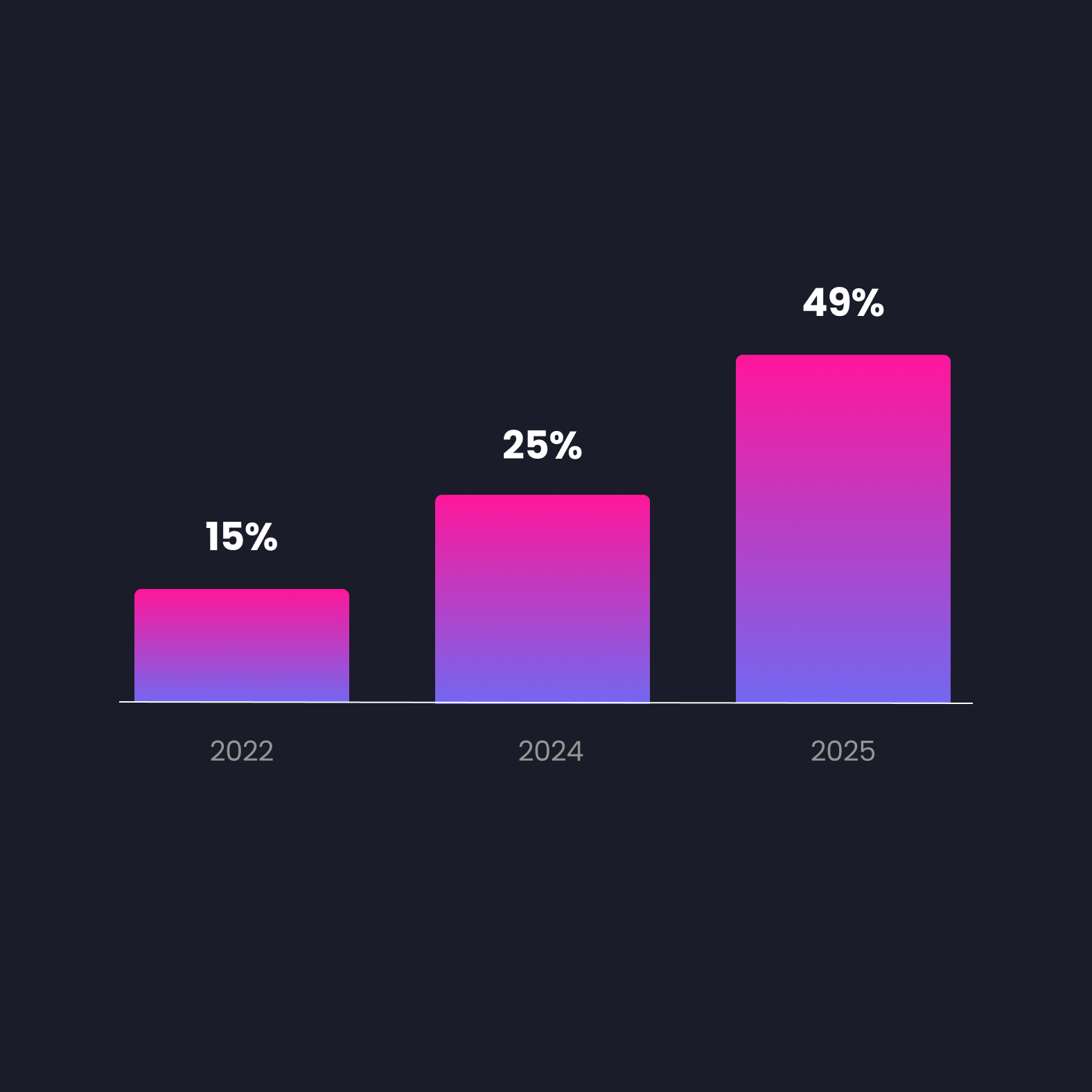
According to the 2026 NASCIO-Deloitte Cybersecurity Study, implementing effectiveness metrics is now the top cybersecurity initiative for 2025–2026, cited by 49% of state CISOs, up sharply from 15% in 2022. KPIs like phishing click rates and incident response time are increasingly used to demonstrate ROI on security investment.
5. Make Secure Behavior the Path of Least Resistance
OLD WAY
Complex controls and heavy-handed policies that employees learn to work around.
NEW WAY
Security designed around how people actually behave, easier to do right than wrong.
When a security control is more painful to use than to bypass, most people will eventually bypass it. Overly complex password requirements lead to reuse, sticky notes, or shared credentials. Clunky MFA flows get turned off or routed around. Approval processes with too many steps get rubber-stamped without review.
Third-Party breach risk is an escalating CISO concern.*
This isn't negligence: it's human nature under pressure. And attackers design their campaigns specifically to exploit the moments when doing the right thing feels like the harder option. Phishing emails are timed when users are distracted. Vishing calls manufacture urgency. The manipulation works because the secure path wasn't made easy enough.
The fix is to flip the equation:
- A well-implemented password manager makes strong, unique passwords easier to use than weak ones.
- Streamlined MFA that integrates cleanly into existing workflows removes the friction that causes opt-outs.
- Security nudges that appear at the moment of a risky decision guide behavior without blocking it.
- Your simulation data helps here too: if a specific team consistently falls for pretexts related to shared document access, that's a signal to look at the workflow itself, not just retrain the people.
Third-party security breaches are now the single biggest projected threat for CISOs in 2026. Much of this exposure originates from employees granting access or credentials under the friction of broken internal processes.
6. Build a Security Culture That Doesn't Divide the Company Into Two Camps
OLD WAY
Security as an IT function, something done to employees, not with them.
NEW WAY
Security culture owned at every level, with leadership modeling the behaviors they expect from everyone else.
One of the most consistent failure modes in security awareness programs is positioning the security team as the adversary. Employees feel tested, judged, and policed. The infosec team becomes the group that sends fake phishing emails and reports who clicked. That's not a culture: it's surveillance with a training label on it.
The goal is cooperation, not division. Employees should understand why they're being trained, know how to report a suspicious call or email without fear of blame, and see the security team as a resource rather than an obstacle. Your best performers in simulations can become internal advocates: They share tips, normalize reporting, and make security feel like something that belongs to everyone. Your worst performers point to gaps in your pedagogy, not just their own behavior.
This also starts at the top. When leadership takes security seriously (participates in exercises, communicates clearly after incidents, and treats simulation data as useful intelligence rather than a scorecard) it sets the tone for the rest of the organization. The CISO's role here is increasingly strategic: translating security risk into business language, building shared accountability across the C-suite, and making the case for investment with data that non-technical stakeholders can understand and act on.
According to the Splunk CISO Report 2026, 79% of CISOs report their role has become significantly more complex, and 96% are now responsible for AI governance on top of their traditional security mandate. Security culture is no longer just a technical problem: It's a business one.
7. Assess Phishing Risk Continuously, Not Just After a Campaign Ends
OLD WAY
Run a campaign, check the click rate, file the report, repeat in three months.
NEW WAY
Continuous risk assessment that tracks individual and team-level risk scores over time and feeds directly into training decisions.
A quarterly phishing campaign gives you a data point. It doesn't give you a risk picture. The click rate you measured in March doesn't tell you how your team will perform in September after a reorg, a product launch, or a period of sustained pressure; all conditions that affect how people make security decisions.
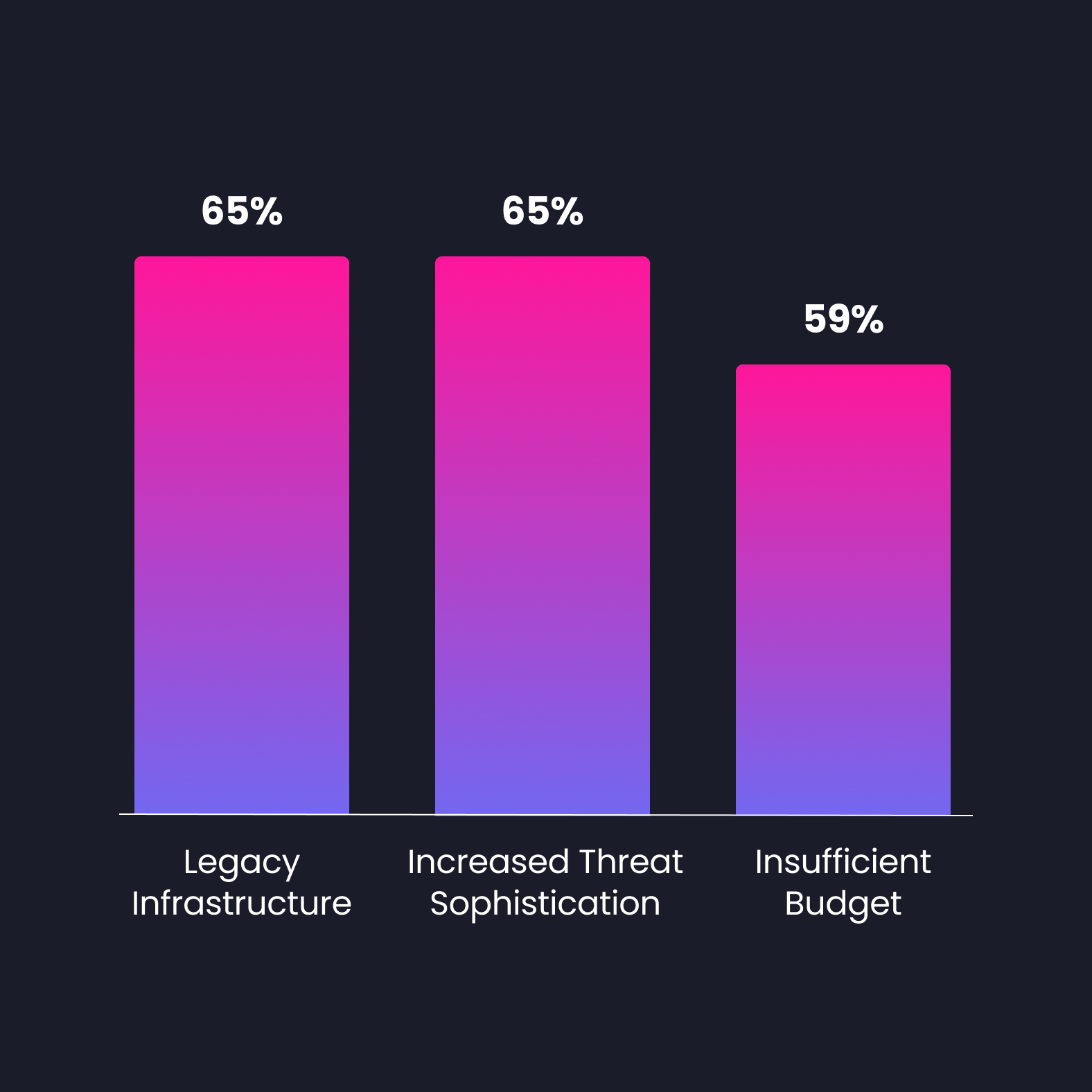
Barriers to CISOs can be eased by strong cyber awareness training and reporting.*
Continuous phishing risk assessment treats susceptibility as a dynamic metric, not a periodic grade. It tracks trends over time, surfaces high-risk individuals and departments before an incident occurs, and connects simulation results directly to training interventions. Instead of telling everyone to redo the phishing module after a bad quarter, you target exactly where the gap is and what content will address it.
This also changes the conversation with leadership. Instead of presenting a quarterly click rate with limited context, you show a risk trend (improving, stable, or deteriorating) and connect it to specific actions your team has taken. That's how security investment gets justified. And that's how the security function moves from cost center to business enabler.
Increasing threat sophistication and insufficient cybersecurity budget are among the top barriers CISOs face in 2026. Continuous, data-driven programs help make the case for resources by demonstrating measurable risk reduction over time.
Old Way vs. New Way
| Security objective | Old way | New way |
|---|---|---|
| Awareness training | Annual e-learning, same content for everyone | Continuous micro-training, role-specific and contextual |
| Phishing simulations | Generic templates, company-wide | AI-driven, role-based, adaptive to past results |
| Attack vector coverage | Email only | Multi-channel: phishing, vishing, smishing |
| Risk measurement | Incident count | Behavioral metrics and continuous risk scoring |
| Security UX | Complex controls, high friction | Secure path = easiest path by design |
| Culture and ownership | IT-led, compliance-driven | Cross-functional, leadership-modeled |
| Risk assessment | Quarterly campaign reports | Continuous monitoring with individual risk trends |
*All stats showcased in this guide are sourced from the 2026 NASCIO-Deloitte Cybersecurity Study and the Splunk CISO Report 2026.
Ready to Build a Program That Goes Beyond Compliance?
Improving your security posture is not a one-time project. It requires understanding how your people make decisions, exposing them to realistic threats across every vector (including voice phishing) and measuring real behavioral change over time.
That's exactly what Arsen is built for: AI-powered phishing and vishing simulations, continuous risk scoring, adaptive micro-learning, and reporting that speaks the language of your leadership team.
See how Arsen supports real cybersecurity culture change →