In cybersecurity, smishing refers to any attack where an SMS, text message, or messaging-app message serves as the pretext or central component of a broader social engineering scheme. According to the Verizon 2025 Mobile Security Index, 80% of organizations reported SMS-based phishing attempts targeting their employees; and the threat is getting more complex. Proofpoint research found that only half of suspected smishing messages even contained a malicious URL. That means the other half relied purely on manipulation, conversation, and trust.
Static, one-shot awareness tests aren't built for this. Defending against modern smishing requires training employees to recognize sophisticated, multi-step, multi-channel attack scenarios, not just spotting a dodgy link.
Key Takeaways
- Smishing is no longer just a link in a text. Nearly half of SMS-based attacks carry no URL at all: they rely entirely on social engineering.
- Financially motivated groups like Scattered Spider have turned smishing into a repeatable enterprise attack playbook, targeting telecoms, SaaS providers, hospitality, and financial services.
- The 4 dominant SMS attack patterns are: MitM OTP hijacking, Reply-to-Verify loops, conversational social engineering, and cross-channel escalation (SMS → email or phone).
- Standard awareness training doesn't cover these scenarios. Most simulations test for clicks; modern attacks test for trust.
- Effective defense requires scenario-based, multi-channel simulations that mirror real attacker behavior, including fake MFA flows, conversational manipulation, and hybrid kill chains.
SMS at the Heart of Modern Phishing Campaigns
Financially motivated threat groups like Scattered Spider (tracked under aliases including UNC3944, Octo Tempest, 0ktapus, and Storm-0875) have made smishing-led attacks their signature move. Their targets span enterprises, SaaS platforms, telecoms, BPOs, hospitality brands, and financial services firms.
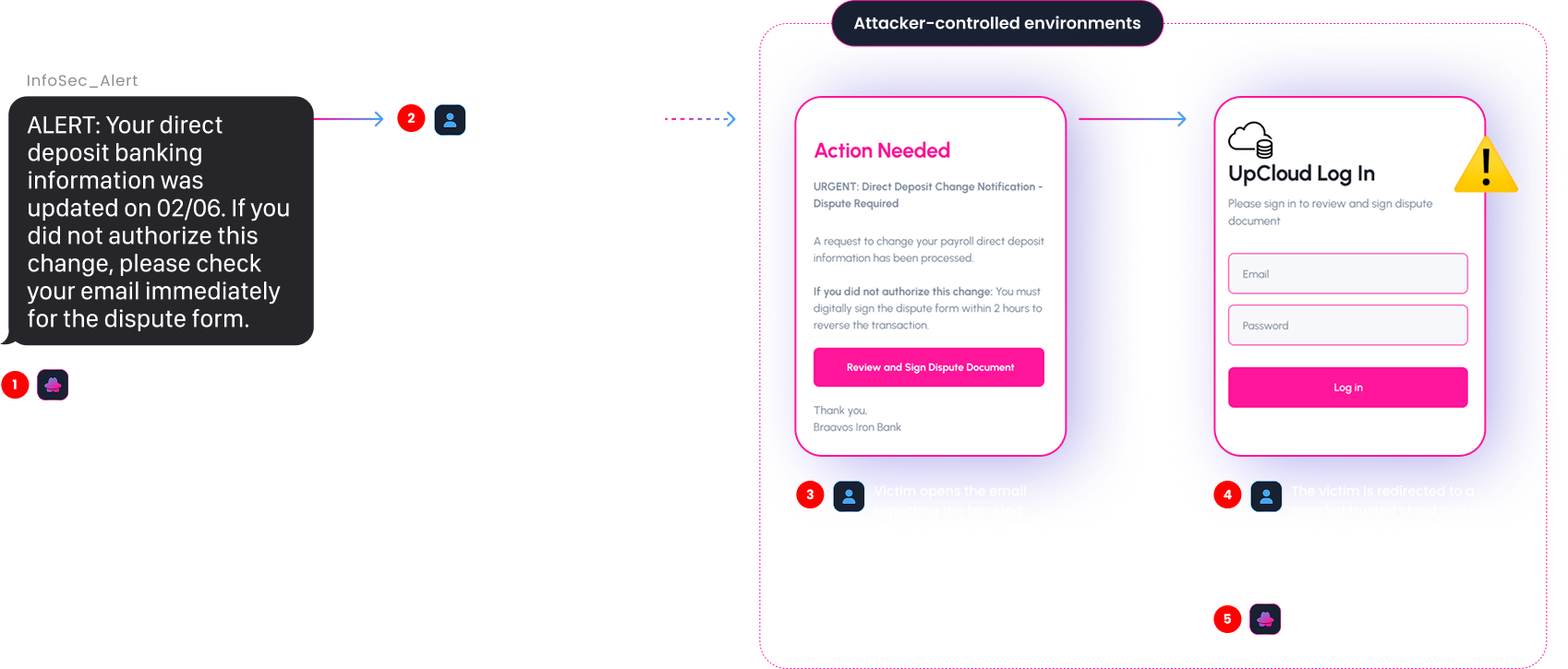
What makes these campaigns so effective isn't any single technical exploit. It's the sequencing: a text message primes the target, an email or phone call delivers the payload, and a fake MFA prompt seals the compromise. Each step looks plausible on its own. Together, they bypass most conventional defenses.
The 4 Most Common SMS-Based Social Engineering Attack Scenarios
Attackers use text messages in different ways depending on what they're after, as an entry point, a keystone, or a trigger for action. Here are the four scenarios security teams need to train for.
MitM SMS OTP Hijacking
Also called Adversary-in-the-Middle (AiTM) phishing, this technique uses reverse-proxy toolkits to sit between the victim and a legitimate login portal. The victim enters their credentials and any MFA code (including SMS OTP) into what appears to be the real site. The proxy relays everything in real time and captures the resulting session cookie. At that point, the attacker has a live authenticated session, without needing password reset.
In this scenario, the attacker already has the victim's credentials and uses a phishing page (not 'real' smishing) to intercept the MFA step. While the SMS OTP the victim receives is legitimate, the attacker's proxy captures and replays it in real time to gain full account access.
In some campaigns, attackers go one step further: once inside, they register their own phone number as a new MFA device to ensure continued access.
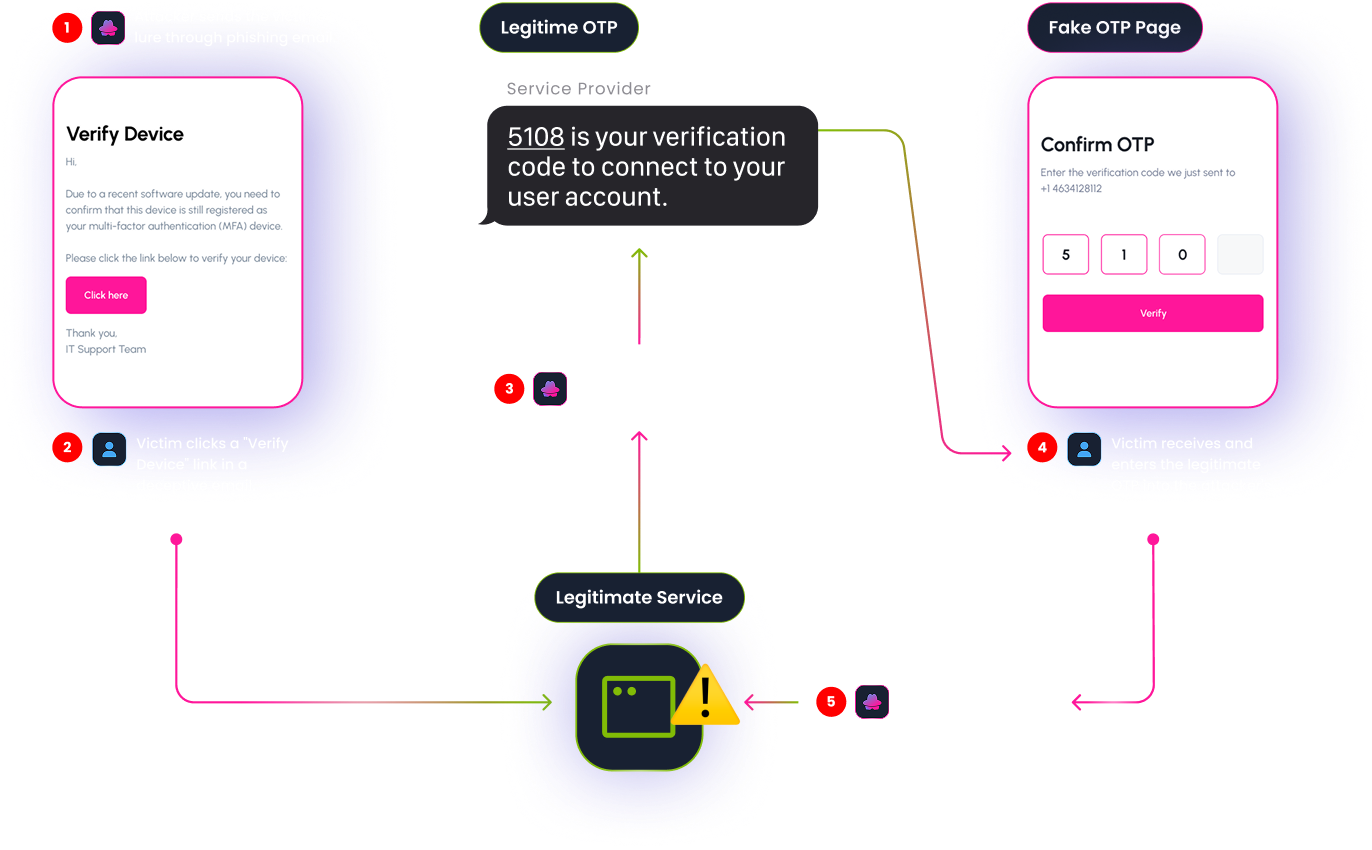
Documented example: Microsoft Defender Experts documented multi-stage AiTM + BEC campaigns targeting banking, financial services, and energy organizations. The attack chain typically began with a compromised vendor email or a file-hosting link redirecting to an AiTM portal, resulting in account takeover without the attacker ever touching the SMS channel directly.
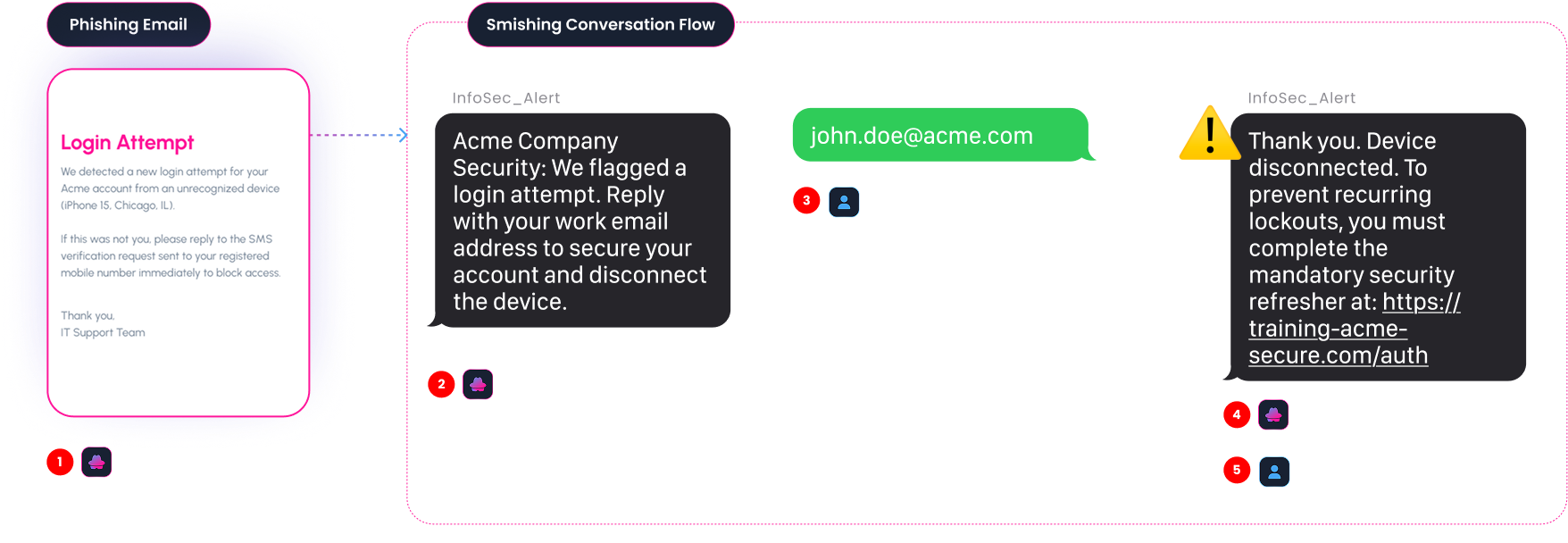
The "Reply-to-Verify" Loop
Here, an email or message initiates what looks like a routine security check, but the "verification" step is actually an SMS conversation designed to build trust before delivering the real payload. The attacker's goal is to establish credibility through a back-and-forth exchange before the victim encounters anything that might trigger suspicion. By the time a malicious link appears, the interaction already feels legitimate. This makes the Reply-to-Verify pattern one of the more durable enterprise threats: it's slow-burn, low-noise, and difficult to detect with automated tooling.
Conversational Social Engineering
No links. No attachments. Just a text message, and an LLM-generated conversation designed to extract information piece by piece. These attacks are particularly effective when the attacker already holds partial credentials or account data. Rather than forcing a technical bypass, they simply ask for the missing piece, wrapped in a convincing pretext: an IT support request, an HR follow-up, a "routine account verification."
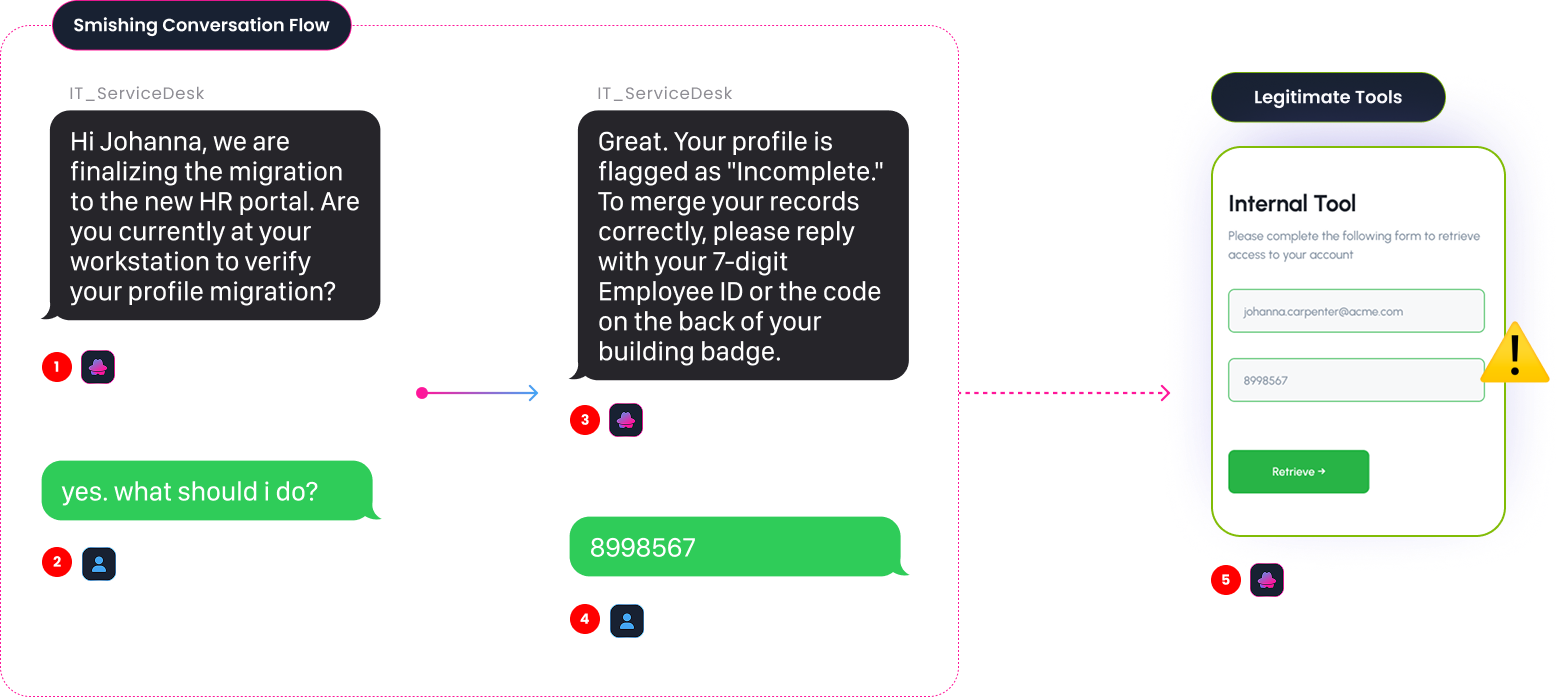
While they might appear less sophisticated than AiTM campaigns, conversational smishing attacks are harder to train against, because the warning signs are subtle and the interaction feels mundane. There's nothing to click, nothing to scan, just a persuasive stranger with the right context.
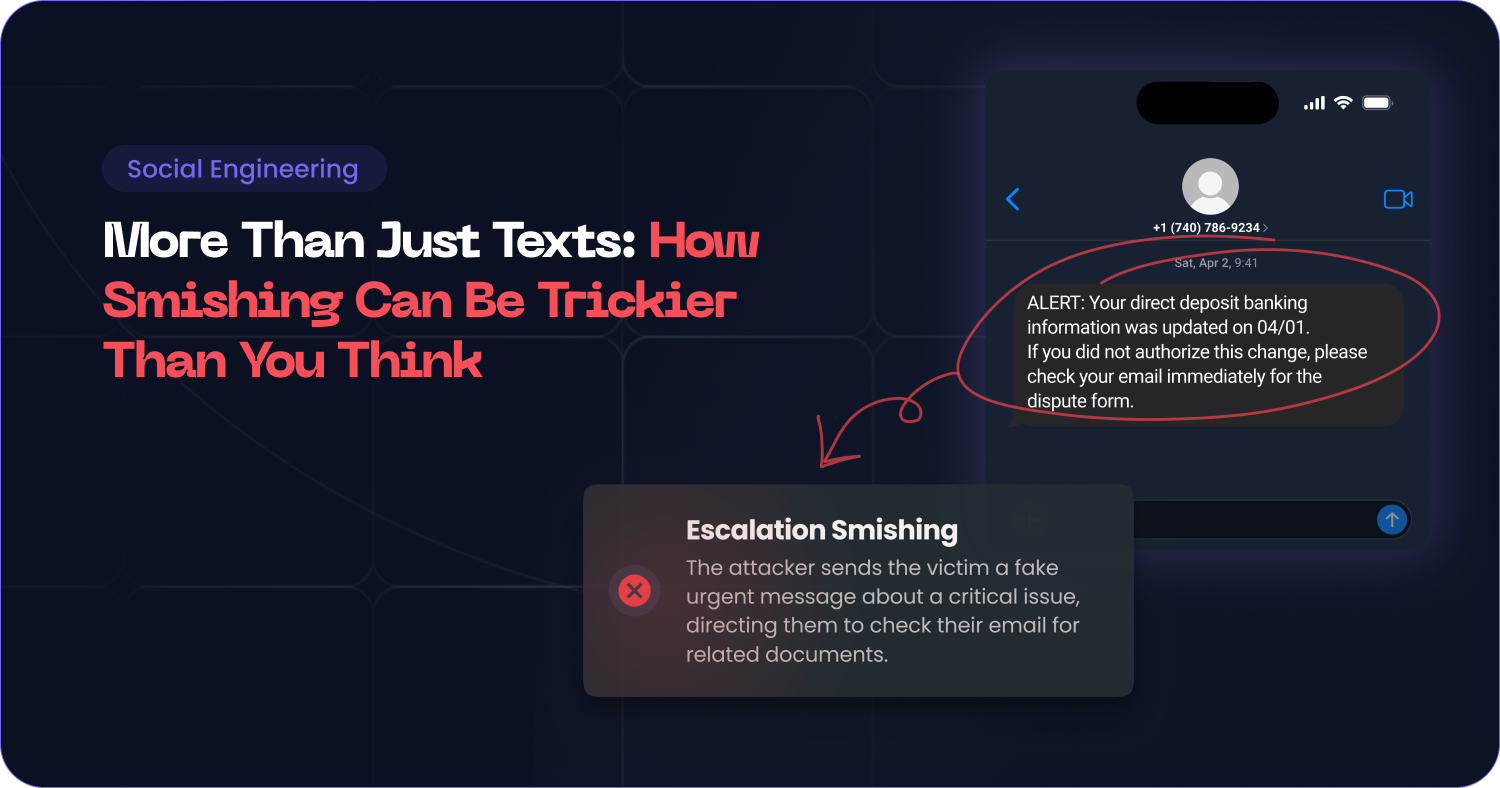
Cross-Channel Escalation
In cross-channel escalation, the SMS message isn't the attack: it's the setup. A carefully timed text creates urgency ("Your account has been flagged - urgent action required") so that when a follow-up email or phone call arrives moments later, the victim is already primed to respond.
This convergence of channels (SMS to email, or SMS to vishing call) is the hallmark of the most sophisticated enterprise campaigns on record.
Documented examples:
- Mandiant (UNC3944 / Scattered Spider): The group's signature tactic is smishing employees with IT alerts ("password expired," "urgent account action required"), then immediately following up with vishing calls to help desks, impersonating the victim to request MFA bypass or password resets. This chain led to major breaches including the 2022 Twilio attack, which compromised 209 customer accounts and exposed Authy tokens. Mandiant identified this pattern as the primary initial-access vector in the majority of their observed incidents from 2022 onward.
- Microsoft (Octo Tempest): Microsoft tracks the same threat actor using targeted smishing against technical admins and help-desk staff, sending fake SSO portal links via SMS before escalating to social-engineered password resets and SIM swapping. In one documented customer incident, smishing led directly to privileged account takeover, data exfiltration, and a ransomware attempt.
The lesson for defenders: any SMS should be treated as a potential pretext. Password or MFA reset requests should require multi-channel verification against known-good contact numbers, not just a callback to the number that texted you.
How to Fight Sophisticated Smishing
Standard cybersecurity awareness training was designed for a different threat landscape. One-shot simulations that test whether a user clicks a link don't reflect how smishing-led attacks actually unfold. Effective defense requires a fundamentally different approach.
Mirror real attacker behavior.
Modern threat actors use hybrid attack chains, like SMS followed by email, email followed by a vishing call, and fake MFA flows to move past standard defenses. Simulations need to replicate these sequences, not abstract them away.
Test for interaction, not just clicks.
Attackers don't stop at the click. They want access, credentials, and eventually the ability to deploy malware or exfiltrate data. Training scenarios should include conversational elements that simulate AI-generated social engineering and test how employees respond under pressure, not just whether they recognize a phishing URL.
Expose hidden human risks.
Generic simulations miss the nuance that makes real attacks work. Tailored scenarios that mirror internal workflows ("System Update Required," "HR Benefits Verification," "IT Security Alert") surface the high-risk behaviors and user groups that standard tests miss entirely.
Build resilience, not just awareness.
A static failure page after a simulated click doesn't build defensive instinct. Real-time behavioral tracking, tracking exactly where a user fell for the trap, whether at the SMS reply, the landing page, or the credential entry, turns every mistake into an immediate, specific training opportunity.
How Arsen Helps You Fight Sophisticated Smishing
SMS phishing is one of today's fastest-growing cyber threats, and most employees have never been trained to spot the advanced variants. Arsen's simulation platform helps you test and train your team using realistic, scenario-based or AI-generated messages that mirror actual attacker behavior, across channels, across steps, and across the full attack chain.Request a demo →
