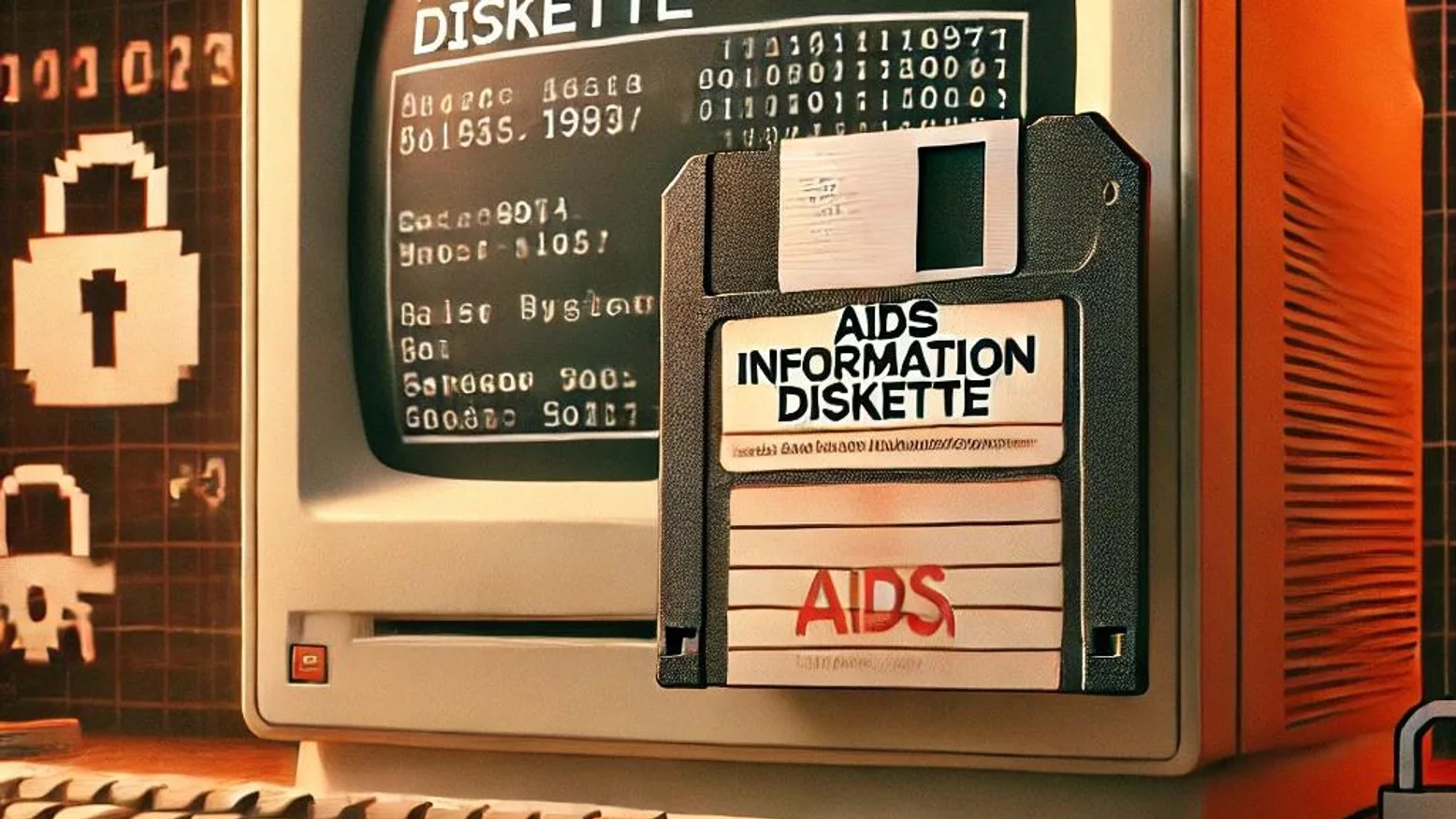
AIDS Trojan Analysis: Early Malware Case Study
The AIDS Trojan, also known as the AIDS Information Diskette Trojan, is widely recognized as one of the earliest examples of ransomware* Its appearance in 1989 shocked the nascent world of...

Remote Access Trojan: What It Is & How to Detect It
Remote Access Trojans (RATs) are a dangerous form of malware that allows cybercriminals to gain unauthorized access and control over an infected computer or network. Understanding the risks posed...

Ransomware Simulator: Testing Your Defenses
In today's cybersecurity landscape, ransomware remains a top threat to organizations of all sizes. A ransomware attack can lock down your systems, encrypt your data, and demand a hefty ransom for...

Locky Ransomware Explained: Protection Strategies
Locky ransomware is a notorious form of malware that emerged in 2016, targeting businesses and individuals alike. This sophisticated ransomware spreads primarily through malicious email...

Ransomware Definition: What is it & How to Secure your Data?
Ransomware is one of the most prominent cyber threats today, targeting both individuals and organizations alike. In this article, we will dive into the ransomware definition, how it works, and the...

Ransomware Attacks: Effective Defense Strategies
Ransomware attacks have rapidly become one of the most disruptive forms of cybercrime, targeting businesses of all sizes. By encrypting valuable data and demanding a ransom for its release, these...

Solutions against ransomware: how to protect, prevent and fight them
Ransomwares are becoming increasingly present on our systems. Reveton, WannaCry, Cryptolocker, REvil: if you know these names, it's because they are all ransomwares that have caused significant...

What is Cryptolocker? Presentation, infection and defence strategies
Cryptolocker is a notorious type of ransomware that has become a major threat in the world of cybersecurity. This malicious software is designed to encrypt a victim's files and demand payment,...

Emotet: the malware that disrupted the private sector for 7 years.
Originally, Emotet was a banking Trojan malware. Its role was to discreetly infiltrate computers in order to steal sensitive information such as banking details. The malware carried out malicious...

WannaCry, the biggest ransomware heist in history
WannaCry is the ransomware behind one of the most significant ransomware attacks. In this article, we look back at the history of this particularly virulent ransomware.