
Microsoft 365 and Azure Social Engineering Threats You Need to Know About
The FBI and Microsoft both flagged active attacks against M365 and Azure in May 2026. Both bypass MFA. Neither uses malware. Both start with social engineering.
MITRE Fight Fraud Framework (F3): What It Is and Why It Matters
The MITRE Fight Fraud Framework (F3) is a structured, analyst-built knowledge base of tactics, techniques, and sub-techniques used by fraud actors in cyber-based financial fraud incidents....
VENOM: Inside a C-Suite Credential Theft Campaign That Neutralizes MFA
Abnormal Intelligence documented VENOM, a previously unknown PhaaS platform behind a five-month campaign targeting C-suite executives across 20+ industries, systematically bypassing MFA to...
From a CEO Impersonation, a Slack Lure to a Full-On Compromise: The Axios & UNC1069 Case
The recent Axios npm supply chain attack, attributed to UNC1069 (suspected North Korean actors), was not a technical exploit. It was a meticulously crafted social engineering campaign. From a...
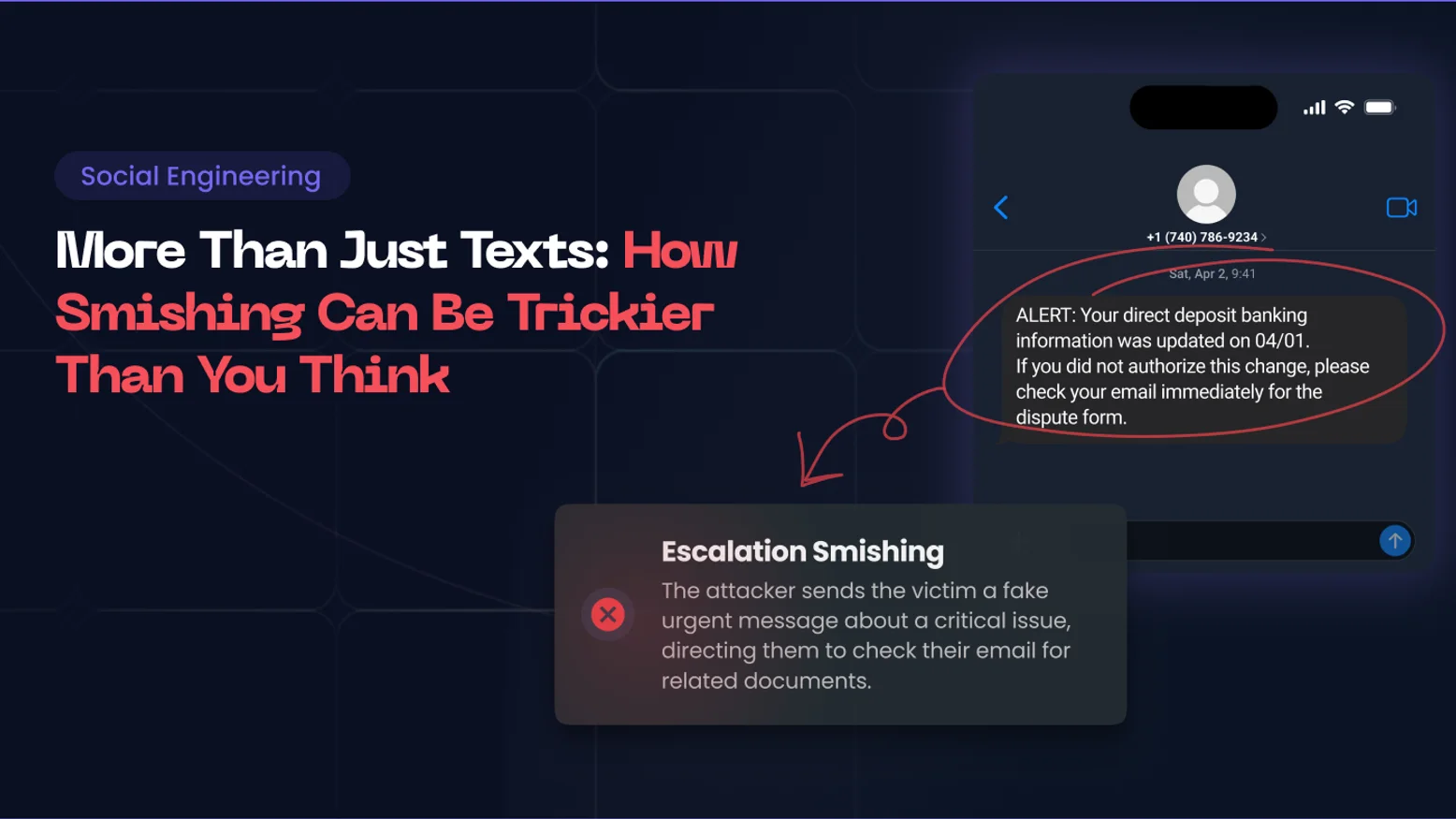
How to Defend Against Advanced Smishing Attacks (and Why Basic Training Isn't Enough Anymore)
Smishing has moved well beyond a fraudulent text. From MitM OTP hijacking to cross-channel escalation, here's how sophisticated SMS-based attacks work, and what it takes to stop them.
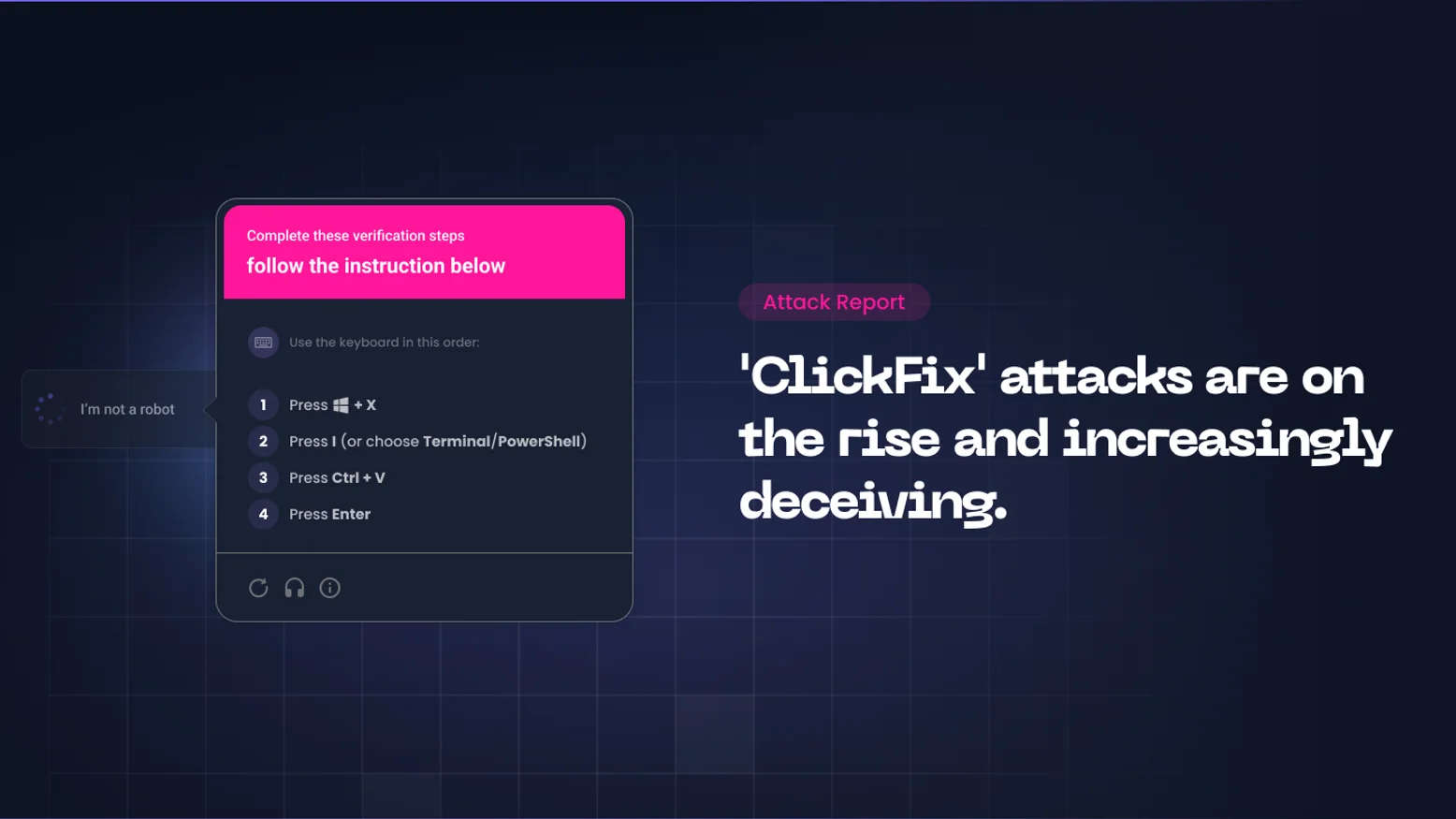
ClickFix Attacks: How Hackers Make Your Employees Run Malware Themselves
ClickFix is one of the fastest-growing social engineering attack techniques. It needs no exploit, no malicious attachment, just a fake error message and a willing user. Here is what happened, why...
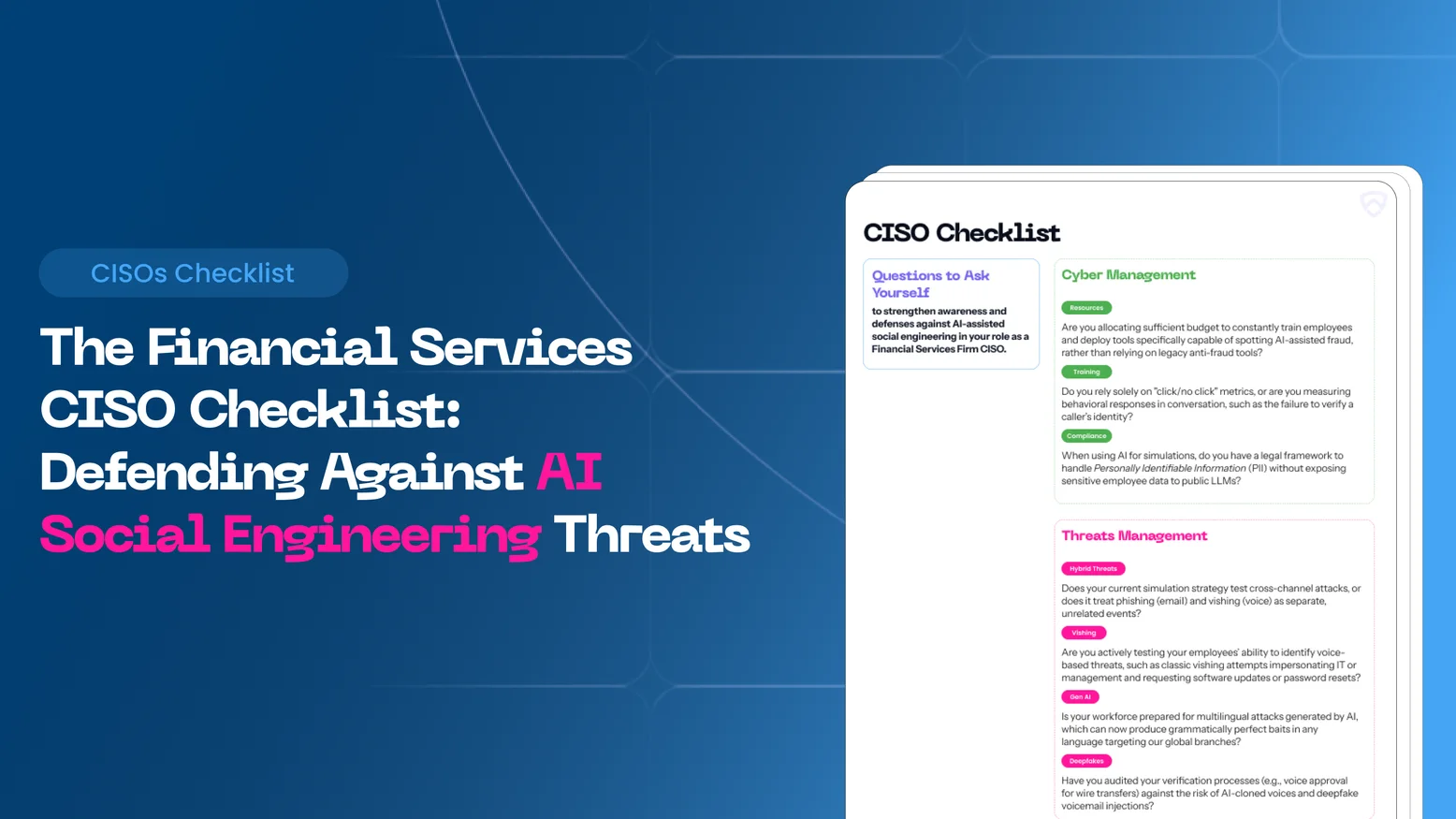
AI-Powered Social Engineering in Financial Services: What Every CISO Needs to Know in 2026
AI-powered social engineering is reshaping the threat landscape for banks, insurers, and fintechs. This guide gives financial services CISOs the frameworks, checklists, and strategic intelligence...

Figure Data Breach: Social Engineering Actors Are Preying on Fintechs, but It’s Not a Fatality
Blockchain lending firm Figure confirmed a significant data breach resulting from a social engineering attack on an employee, leading to the leak of customer data and highlighting the persistent...
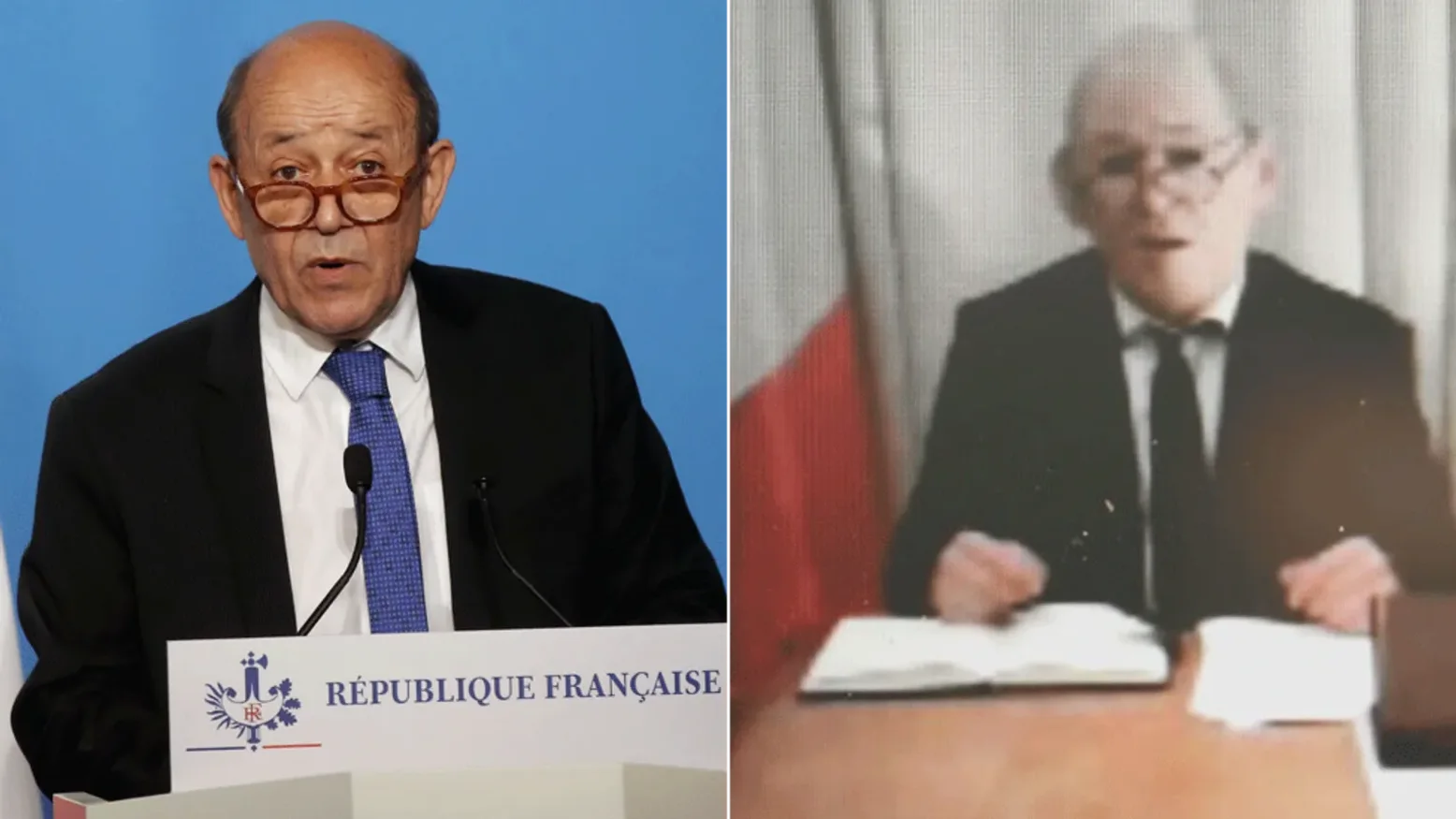
The Le Drian Scam: A Masterclass in Social Engineering
Social engineering, the art of manipulating individuals to divulge confidential information or perform actions that compromise security, has evolved dramatically in recent years. But before...

Social Engineering Attacks: Tactics and Defenses
In this article we’ll explore how people’s emotions become business vulnerabilities, why social engineering is so effective, and three powerful principles to secure and protect your environment.

Social Engineering Examples: Real-World Tactics
How can you protect your organization from social engineering attacks and their adverse impacts? This article explores different attack strategies, real-world examples, and prevention methods.
How Do People Get Doxxed? | Risks and Prevention Tips
Doxxing, short for “document tracing,” refers to the act of publicly disclosing someone’s personal information, like their real name, home address, phone number, or even financial data, without...

Pretexting Definition: The Art of Deceptive Information Gathering
Pretexting is a social engineering tactic that involves creating a fabricated scenario to deceive an individual into disclosing sensitive information. Unlike other forms of cyberattacks,...

What is Pretexting? | Understanding Social Engineering
Pretexting is a sophisticated social engineering technique used by cybercriminals to manipulate individuals into divulging sensitive information. But what is pretexting exactly, and how does it...
Social Engineering Definition: Cybersecurity Best Practices
Social engineering is a technique used by cybercriminals to manipulate individuals into revealing confidential information or performing actions that compromise security. Rather than hacking...

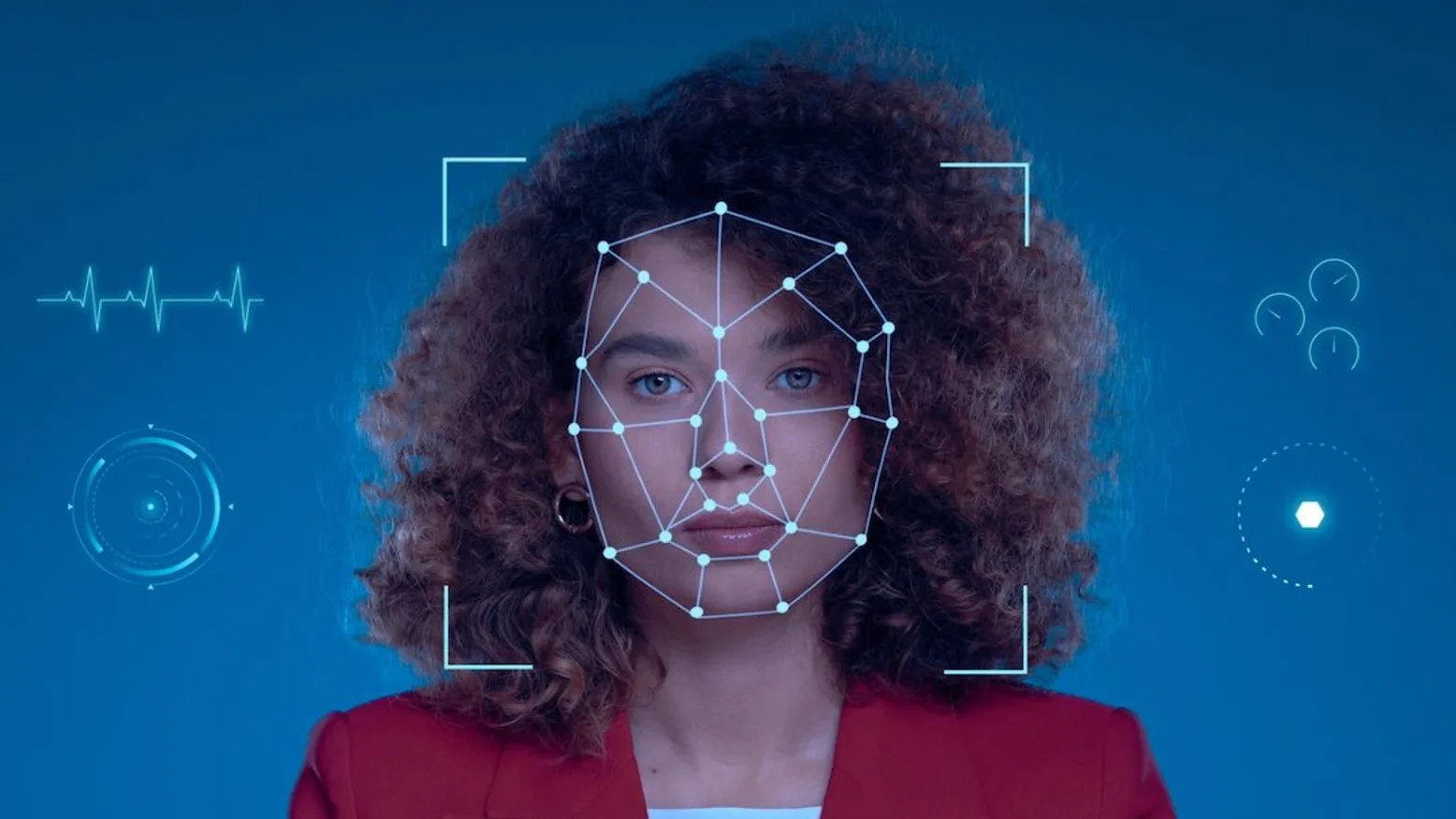
PII Meaning — What It Is & How to Protect Personal Data
In today's digital world, the term "PII" (Personally Identifiable Information) has become central to discussions around cybersecurity and privacy. But what exactly is PII, and why is it so...
What is Doxxing? | Understanding Online Exposure
In today’s digital age, personal information is more accessible than ever, and this has given rise to a dangerous practice known as doxxing. But what is doxing? Simply put, doxxing (also spelled...

PII (Personal Identifiable Information): How to Protect Your Privacy?
In today’s digital age, Personal Identifiable Information (PII) is more vulnerable than ever. With cybercriminals targeting sensitive data to commit identity theft or fraud, safeguarding your PII...
Catfishing Definition: What It Is & How to Spot the Signs
In March 2021, the top 10 dating sites in France recorded 46.4 million visits, according to a study conducted by [monpetitdate](https://www.monpetitdate.fr/etude-statistiques-sites-de-rencontre/)....