Arsen Security Blog
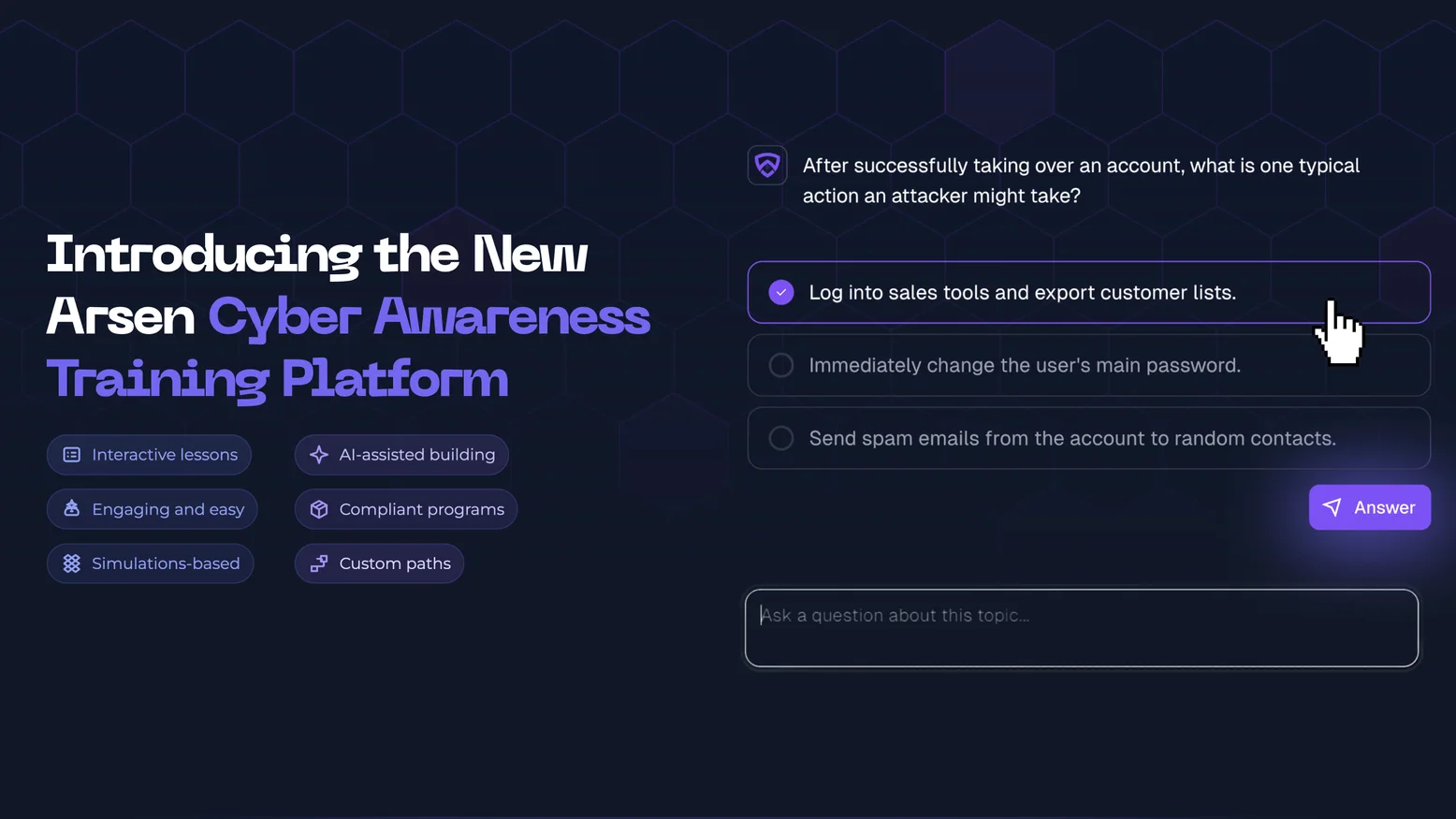
Introducing the New Arsen Cyber Awareness Training Platform
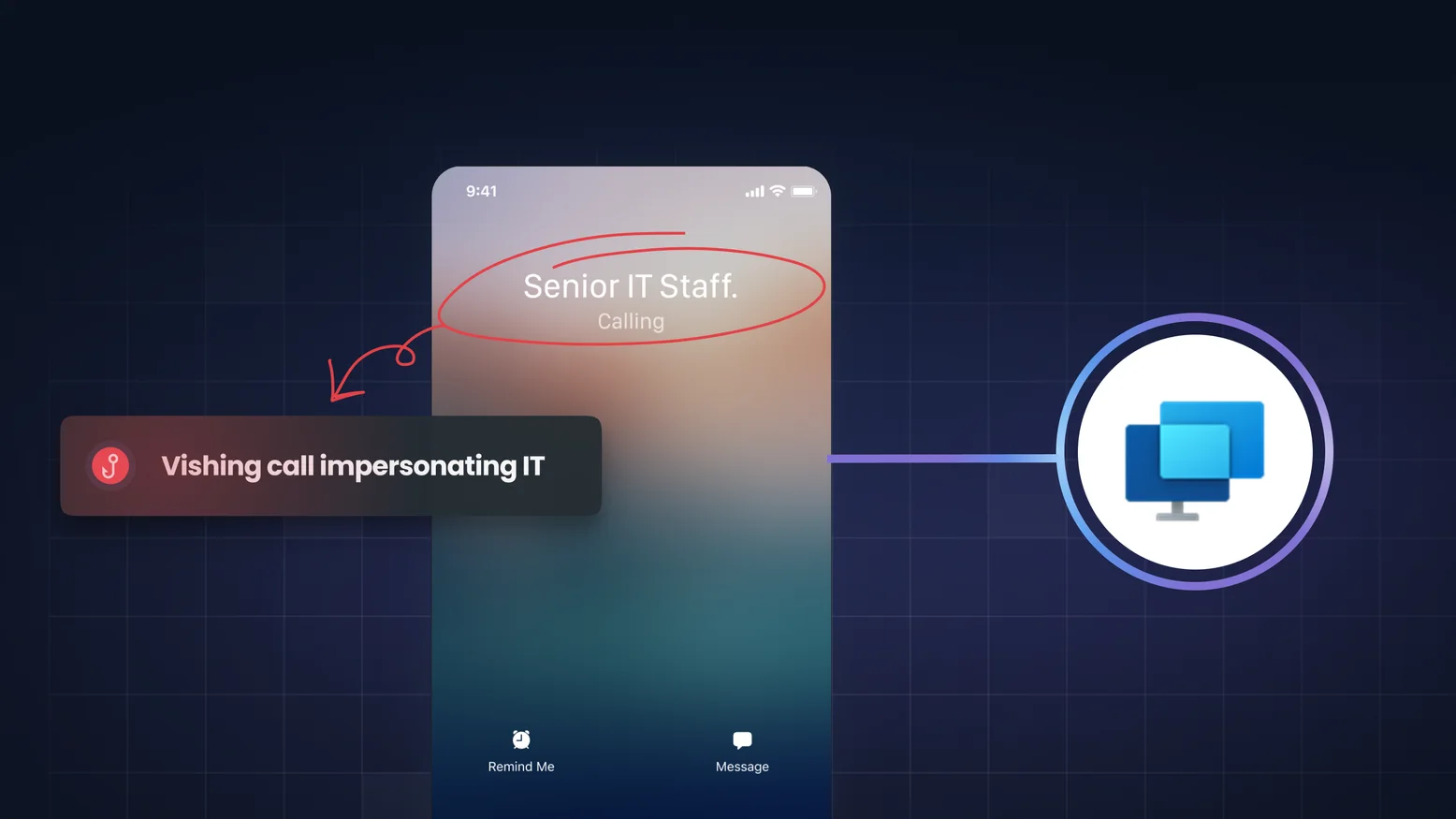
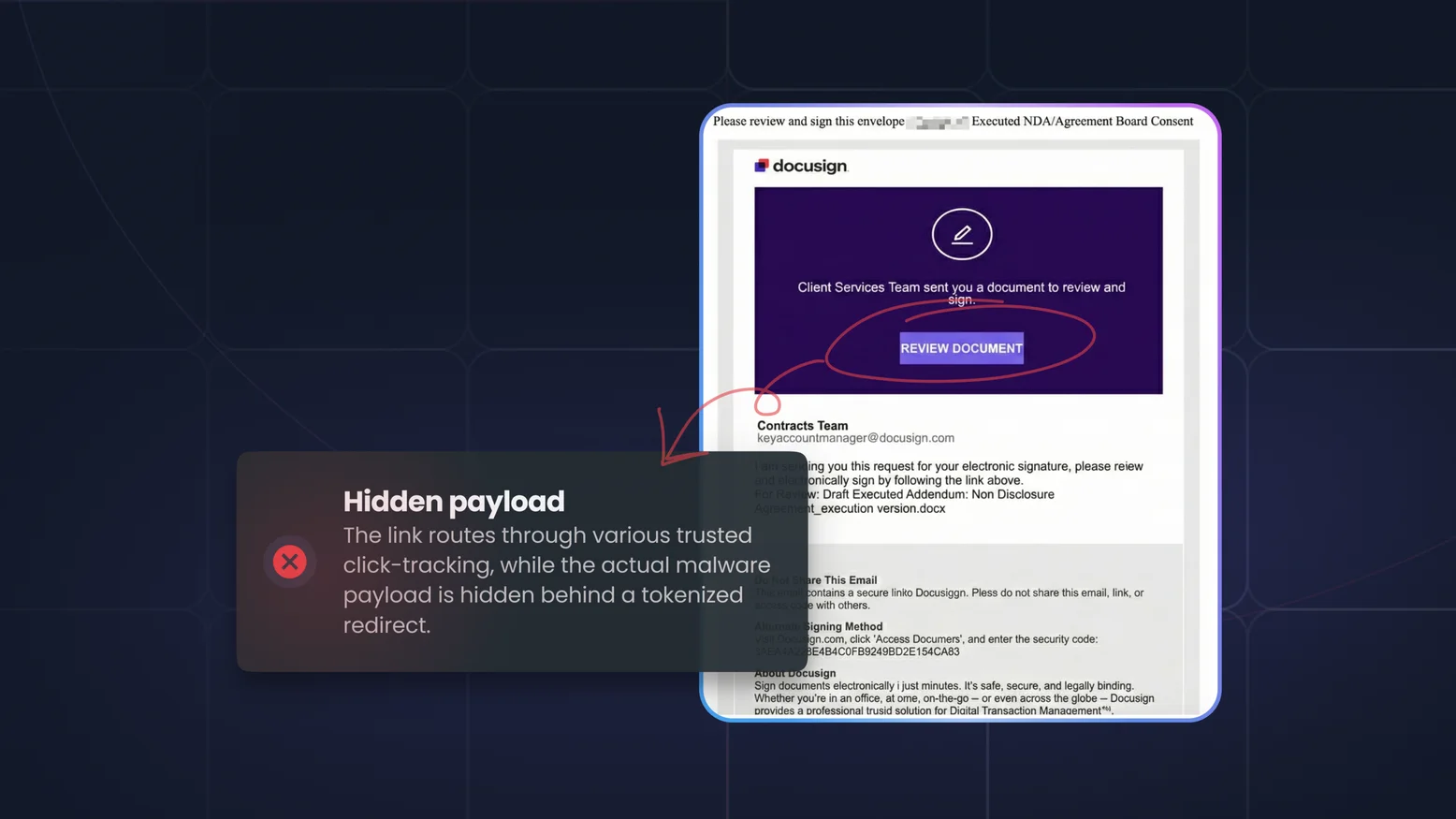
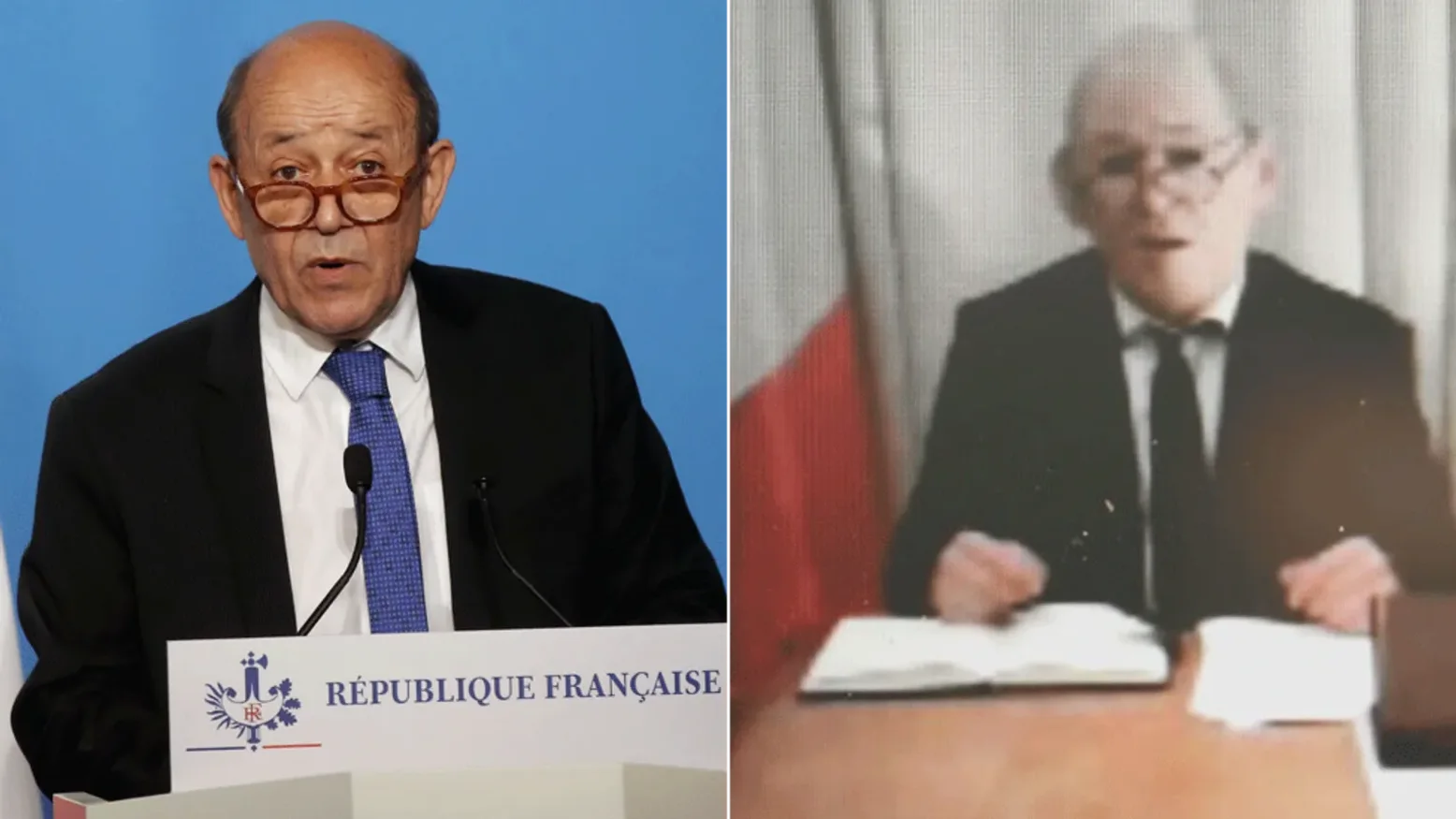
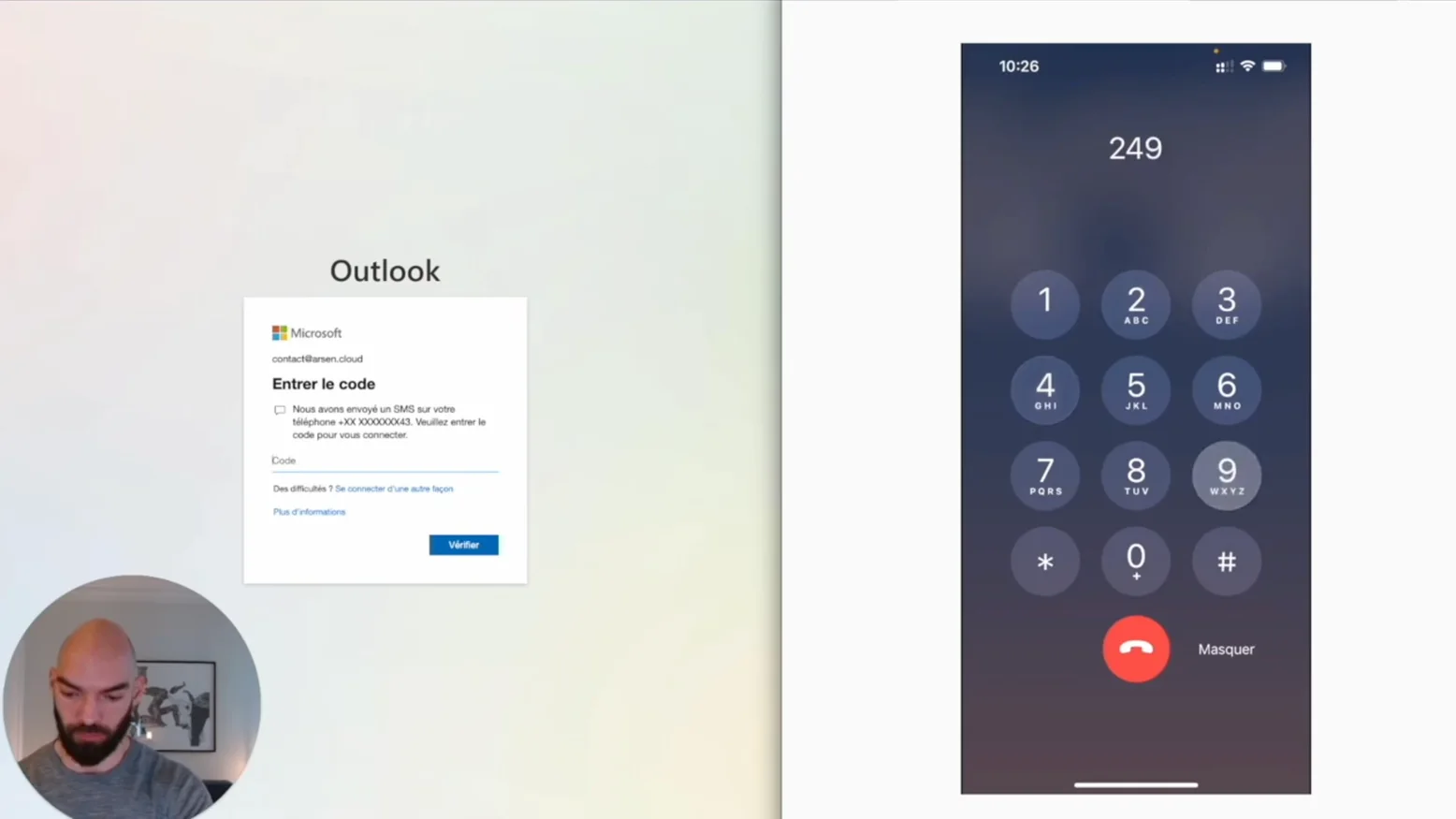
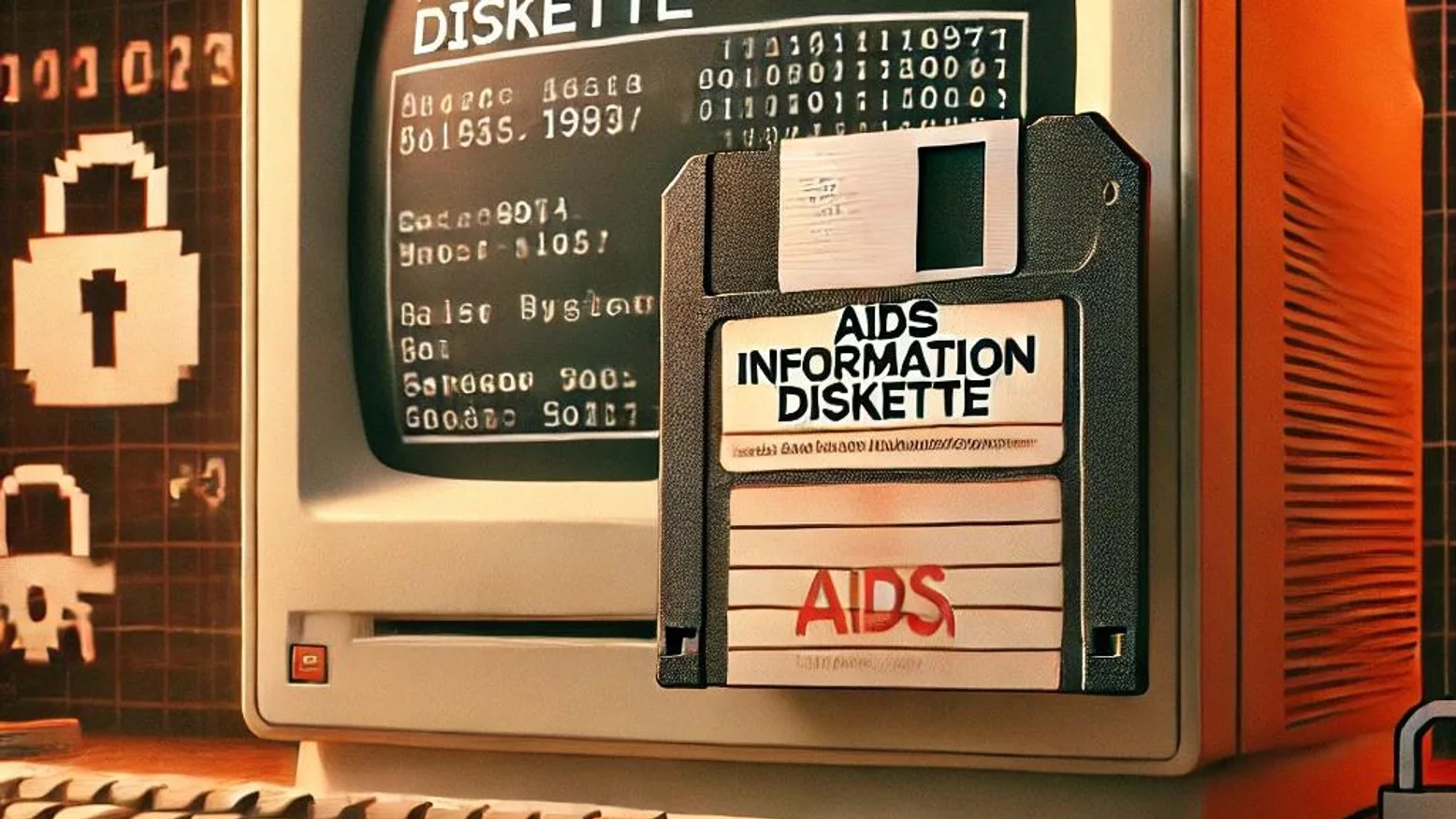
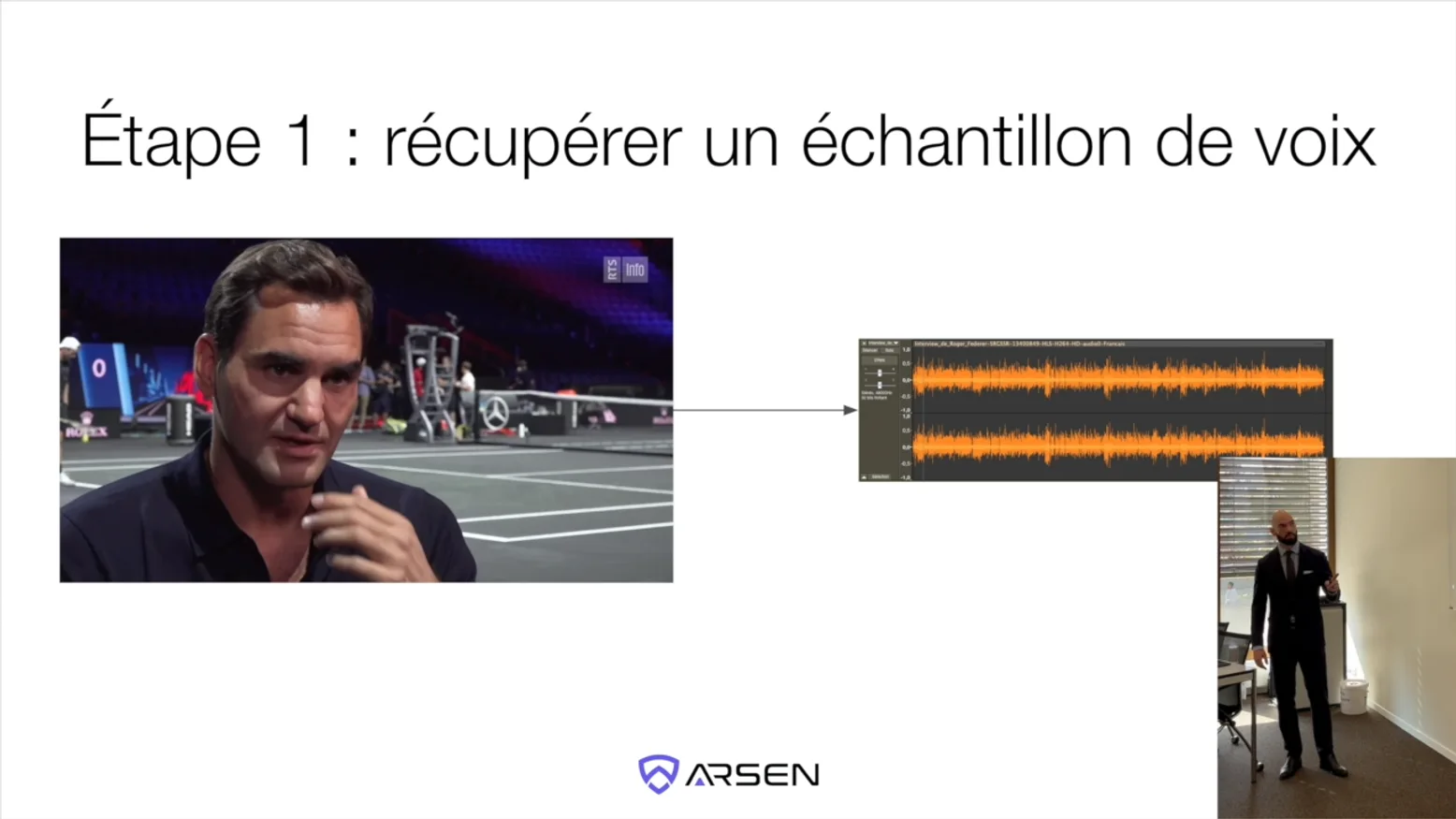
For the past few weeks, we’ve been gradually deploying a redesigned security awareness training module, progressively available to all customers. We have designed our new training module specifically for the AI era. It moves beyond static compliance content to deliver...